Compliance Risk Management: The Complete Guide
For companies that face risk from potentially violating laws or regulations, having a compliance program in place reduces this risk. A compliance risk management program enables the company to show it’s following the required rules, so that any compliance violations can be clearly shown as accidental–and immediately remedied.
What Is Compliance Risk Management Anyway?
Almost any kind of organization, whether it’s private or public or whether it’s for-profit or non-profit, must comply with certain regulations. The size of the company doesn’t really matter much when it comes to compliance risk management, either. Companies have to follow the required regulations for their industries.
As a general definition, compliance risk management involves the process of identifying potential risks of noncompliance with these regulations for a company. Through proper risk management, companies are able to anticipate these risks, and then take the steps necessary to avoid having them actually occur.
Risk Management Isn’t Perfect
Even the most stringent—and expensive—compliance risk management programs probably won’t catch every potential risk. Keeping up with regulatory changes and monitoring every potential issue is incredibly challenging.
With this in mind, a successful risk management program simply attempts to reduce the risks to the lowest possible level.
Those implementing risk management programs strive for perfection. However, they understand that reducing the potential for risk to the lowest possible level that matches the standard for the company’s industry is an acceptable result.
What Happens If a Company Doesn’t Reach Compliance?
The risks of failing to comply with regulations, standards, and laws will depend on the industry standards in place. Penalties potentially include legal charges, fines, negative public relations results, and loss of material goods.
Because risk management rarely delivers perfect results, many companies explore risk management compliance with an eye on finding the area with the biggest risks. These often are the areas with the biggest potential penalties too.
They can start working on those areas first and can expend the most resources there, ensuring they have the best possible coverage where they need it the most.
How Compliance Risk Management Works
Implementing compliance risk management can involve making use of a few different tools. These may include qualified current staff members, new hires, software packages, and third-party vendors. Companies can use a combination of these tools if desired.
Using Employees
Companies always have the option of performing risk management with current staff members or with hiring a few new people. Typically, a company will choose this option when it wants to have full control over the process. This represents the traditional way of handling risk management compliance.
It can be a cost-saving measure to use in-house employees. However, if employees are already busy and have other job responsibilities, risk management processes may not receive the attention they need.
Another danger of using current employees is that they may fall into the habit of continuing to use the same processes they’ve used for many years. For the best level of success, a company must be willing to adapt to the changing needs of risk management. They must be willing to implement new processes and tools to provide better results.
Using Vendors
Many third-party vendors will provide compliance risk management services on a contractual basis.
For a company that doesn’t want to hassle with the risk management process, or that doesn’t feel comfortable doing it alone, hiring a vendor is a safe and effective option. However, the costs of using vendors can add up quickly.
Some vendors will have expertise in a certain area of compliance. A company may want to hire a vendor for a particularly important type of compliance it needs. It then can handle the other compliance requirements with in-house employees.
Using Software
For companies that will handle the compliance risk management process at least partially in-house, using software can be a helpful additional tool.
Without software, risk management documentation can take on a variety of formats with multiple styles of writing. Compliance software provides a means of maintaining consistency in documentation quality. Having proper documentation is an important step in maintaining compliance with government standards.
Another advantage of compliance software is that it provides constant monitoring and tracking of risks. The data obtained through the software helps a company find potential issues. The company doesn’t have to wait until it runs its weekly or monthly test to learn of an issue when the software is providing constant monitoring.
Making use of risk management software will bring an extra expense. But it also provides time-saving, automated features. In-house employees won’t have to do as much manual work to run compliance risk management procedures. This saves on personnel costs.
Protecting Against Risk
A company can select one or more of these tools to manage its risk. The collection of tools needs to handle the situations specific to the company’s industry that result in noncompliance. Some of the most common examples appear below.
Example 1: HIPAA and Medical Records
One of the most important aspects of risk management in the healthcare industry involves following HIPAA compliance regulations. HIPAA, short for the Health Insurance Portability and Accountability Act, is a set of requirements for protecting sensitive patient data and medical records.
The HIPAA regulations work to protect Electronic Medical Records (EMR) and Electronic Protected Health Information (EPHI). This type of data is valuable for hackers who can use it to try to steal identities. The data can include:
- Patient’s full name and address
- Social Security number
- Health history and information
Maintaining HIPAA Compliance
To maintain compliance with HIPAA, organizations must show they have security procedures in place. These security measures work to protect patient data.
HIPAA regulations also require that companies only allow authorized personnel to gain access to the data. Making use of activity logs and audit controls can help a company maintain HIPAA compliance in this area.
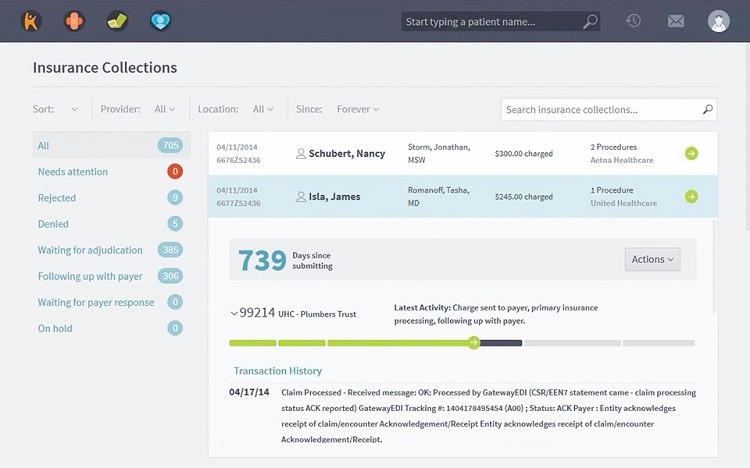
One of the ways to maintain a compliance risk management program that follows HIPAA guidelines is through the use of software. The best Electronic Medical Records software packages, such as Kareo (pictured above), provide at least some capability to maintain HIPAA compliance. Some software packages are fully HIPAA compliant.
Additionally, many third-party vendors will offer to monitor a company’s system for maintaining HIPAA compliance.
Example 2: GLBA and Consumer Financial Information
Companies that handle consumer financial information must maintain the privacy of that information. The Financial Modernization Act, as part of the Gramm-Leach-Bliley Act (GLBA), is a federal law that enforces the required levels of protection.
Businesses like banks, securities firms, insurance companies, loan brokers, debt collectors, real estate appraisers, and others must follow these regulations. Any companies that provide financial products to consumers must comply with GLBA.
The GLBA requires these types of businesses to maintain the security of customer data that fits under the definition of NPI, or nonpublic personal information. Some examples of NPI include:
- Social Security numbers
- Bank account numbers
- Credit card numbers
- Income amounts
- Credit scores
- Name and address
- Contact information
The financial institution can obtain the NPI from the consumer directly through volunteered or provided information. NPI also can come from the results of a financial transaction the consumer performed or from a service the institution performed for the consumer. Regardless of how the financial institution gathered the data, it must protect it under GLBA.
Maintaining GLBA Compliance
Businesses that fail to maintain compliance with the rules of GLBA could face fines up to $100,000 per violation. A major security breach could lead to tens of millions of dollars in fines.
To maintain compliance with GLBA, businesses should have a security plan in place that protects the required data. Security personnel must regularly test and monitor the performance of the system and security plan. Having detailed training procedures in place regarding the handling of sensitive customer NPI data is another requirement of GLBA compliance.
Additionally, the business must provide most consumers with an annual privacy notice regarding how it handles data.
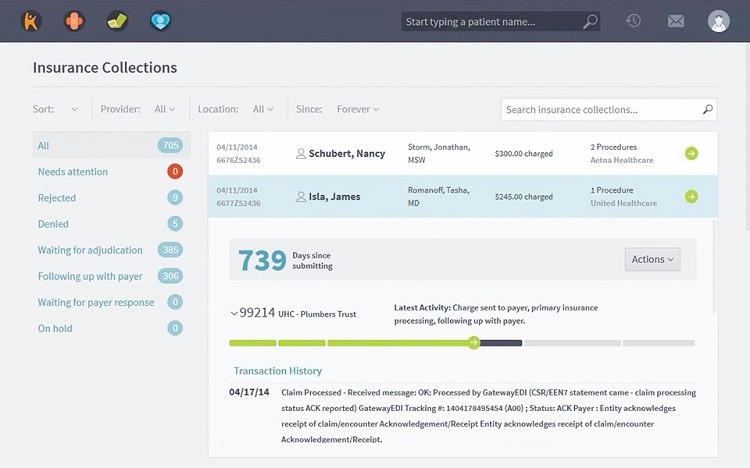
Companies that need to show GLBA compliance risk management policies have the option of using software to monitor and test the system. LogicManager (pictured above) is one software package that handles GLBA compliance risk management procedures. Companies also can hire third-party vendors to maintain the appropriate safeguards of the customer data.
Example 3: FERPA and Student Information
Federal law requires organizations that handle student educational records to have compliance risk management procedures in place to safeguard those records. This protection falls under the Family Educational Rights and Privacy Act (FERPA).
Schools must maintain the privacy of a student’s records. Parents and students have the right to review their educational records at the school, requesting any corrections. Parents lose their right to review the records once the student turns 18 or begins attending an educational institution post-high school.
Exceptions to FERPA
With a few exceptions, to release the records to any third party, schools must obtain written permission from the student or parents. Some of the exceptions include:
- To satisfy judicial orders
- Sending to a new school after the student transfers
- To comply with a financial aid application from the student
Schools can release directory information about students without consent, such as dates of attendance, awards, and honors. Students do have the ability to opt out of the release of this directory information.
Other types of personal data that the school may hold must remain protected under FERPA. These items may include a school ID number, a Social Security number, grades, and health information, barring one of the exceptions listed above.
Maintaining FERPA Compliance
Any school that receives federal funding from the Department of Education must follow FERPA guidelines.
Educational institutions that fail to maintain FERPA compliance could suffer a loss of federal funding. Individuals that fail to protect the information or that steal it could face criminal prosecution.
Additionally, schools must be careful about any student information they share with other companies. Those companies also must protect the data under FERPA guidelines. Any company the school works with should guarantee FERPA compliance.
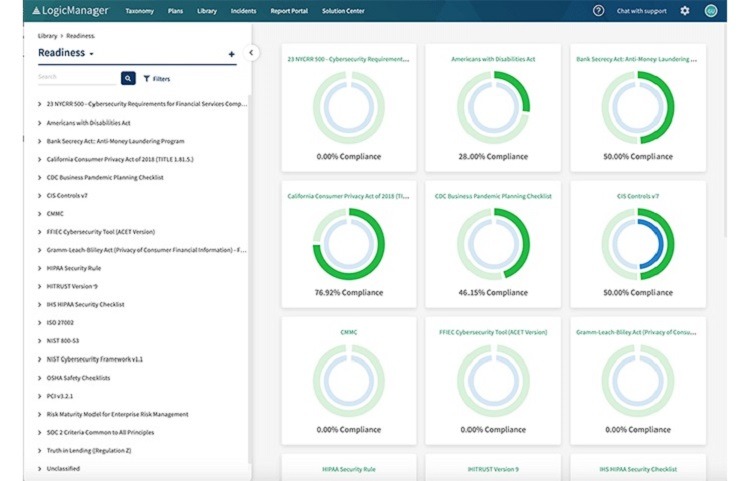
Multiple software vendors, such as Netwrix (pictured above), have the ability to monitor systems at schools and at companies that handle this data to ensure compliance with FERPA. This software can perform audits and can maintain data access logs. Third-party vendors are available to maintain FERPA compliance for schools that hire them too.
Training of staff members about the importance of maintaining FERPA compliance should occur on a regular basis. Having documentation, policies, and procedures in place for staff members is important for meeting compliance regulations.
How to Get Started With Compliance Risk Management
Here are some of the most common steps organizations can follow to start a compliance risk management program.
Working through these steps can help a company determine whether it needs help with setting up a compliance risk program from software or a third-party vendor.
Step 1: Understand Your Industry’s Regulations
Before setting up a compliance risk management program, a company must have detailed knowledge about which regulations and laws it needs to follow. Make sure the company understands any recent changes to the regulations as well.
With these areas identified, companies can then determine which areas are most important. They can tackle those areas first and devote the majority of resources to those areas. There’s no need to waste time and money on regulations that don’t affect a particular company.
At the same time, think about the best ways to implement programs. A procedure in place during the past decade may no longer work as well. Significant changes in the types of risk, thanks to the proliferation of interconnected systems and storage of sensitive digital data, require a new approach in some programs.
Step 2: Determine Who Needs to Participate
Developing a compliance risk management program requires understanding which members of the organization should have involvement. This includes team members who should work with the development of the program and those who should help with implementation, monitoring, and testing.
By having team members from multiple departments participate, it’s easier to understand all of the regulations the company is facing. No regulations or standards slip through the cracks.
Step 3: Identify Which Tools to Use
Companies looking to install a compliance risk management program have a number of tools available to them. Figuring out which tools to use is important for figuring out the potential costs of implementing a program.
Understand that some organizations can handle this process with the staff they already have in-house. Others may need to hire additional employees. Some companies rely on third-party compliance risk specialists and vendors they can hire to help with setting up the program.
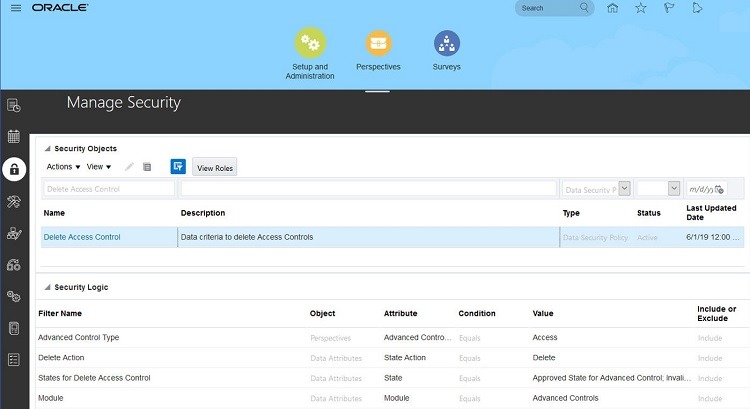
Some companies use business process management software tools, such as Oracle (pictured above) to manage risk compliance.
Companies can use a mixture of all these tools to achieve the results they want.
Step 4: Prepare for Testing and Monitoring
With the processes for compliance risk management in place, the company can begin implementing testing and monitoring procedures. Ideally, the testing and monitoring help the company spot potential risk hazards before they lead to violations.
Testing the system immediately after implementation is especially important. Companies want to catch potential installation and setup errors before team members start using the system and magnify the errors by repeating them.
Step 5: Create and Distribute Documentation
With the compliance risk management procedures installed and running smoothly, it’s time to train the team. The security team needs to create documentation that employees can follow to ensure compliance at all times.
Training and documentation should involve detailed instructions on how to implement any procedures the employees must use. But these items also should set the tone about the company’s attitude regarding compliance. Sloppy training methods and incomplete documentation about compliance will make employees become lazier about following the procedures.
Companies that excel in compliance risk management emphasize the importance of it in all aspects of work. It becomes part of the company culture through repetition and emphasis at all levels.

