NIST SP 800-53 Compliance Checklist
NIST Special Publication (SP) 800-53 defines the best practices for implementing secure information systems to protect sensitive data. Originally published in 2005 to assist government agencies with FISMA (Federal Information Security Modernization Act), the publication has gone through several revisions over the years, and its language today can be applied to any organization that wants to strengthen security protocols.
The NIST SP 800-53 publication is designed to help organizations improve risk management processes by providing them with a catalog of more than 1,000+ security protocols as a resource. These protocols cover every aspect and consideration of an information system—ensuring that the chances of an incident are reduced and incur minimum damage.
All government agencies are required to comply with NIST SP 800-53. Government contractors who manage federal IT networks or operate on federal IT networks will also have these compliance requirements outlined in their contracts.
Whether you’re a government agency, government contractor, or just an organization that wants to improve security protocols, this in-depth guide will help you stay compliant with NIST SP 800-53. Use the compliance checklist below as a resource as you’re implementing new protocols and maintaining existing security standards.
Get Familiar With the NIST SP 800-53 Control Families
NIST SP 800-53 is a collection of security protocols to help organizations safeguard information systems from a wide array of risks. These protocols are segmented into 20 different control families.
To stay compliant with NIST SP 800-53, you must have a firm grasp of these control families and their purpose.
- Access Control (AC)
- Awareness and Training (AT)
- Audit and Accountability (AU)
- Assessment, Authorization, and Monitoring (CA)
- Configuration Management (CM)
- Contingency Planning (CP)
- Identification and Authentication (IA)
- Incident Response (IR)
- Maintenance (MA)
- Media Protection (MP)
- Physical and Environmental Protection (PE)
- Planning (PL)
- Program Management (PM)
- Personnel Security (PS)
- Personally Identifiable Information Processing and Transparency (PT)
- Risk Assessment (RA)
- System and Services Acquisition (SA)
- System and Communications Protection (SC)
- System and Information Integrity (SI)
- Supply Chain Risk Management (SR)
You can refer to this resource from the NIST for more details on the SP 800-53 control families.
Apply Minimum Controls
Each of the 20 NIST 800-53 control families has a minimum control, also known as a baseline control. Minimum controls are used as the basic security and privacy measures that must be implemented to protect information systems.
Applying minimum controls will help an organization meet the specific requirements of that specific control family.
You can view, search, and download the controls and baselines directly from the NIST website.
In addition to the baseline controls, there are also enhanced controls that provide additional protections and functions—building upon the baseline.
While enhanced controls can be used within organizations that have increased risks, baseline controls must be implemented before control enhancements can be considered.
For example, let’s say you’re looking at the incident response control family. The minimum control would cover basic incident management. But an enhanced control would go into more detail on specific incidents, like guidance for coordinating supply chains.
Stay Up to Date With New Revisions
In an effort to keep pace with new threats and best practices, the NIST regularly releases new versions of SP 800-53. Here’s a quick summary of the revision history:
- Initial release in 2005
- First revision released in December 2006
- Second revision released in December 2007
- Third revision incorporated a risk management framework, organization-level security protocols, and guidance for FISMA security standards paired with international standards like ISO/IEC 27001. This was the first major revision since its initial release.
- Fourth revision released in 2012 contained 18 control families
- Fifth revision released in 2020 removed “federal” so regulations can be applied to any organization
There are additional revisions to the newest release, including an A version and a B version.
To stay compliant, you need to make sure that you’re referring to the right resources. For example, if you’re using the fourth reversion as a reference, you’ll only see 18 control families. But the newest version contains 20 control families.
Organizations have one year from the release date of a new reversion to comply with updated NIST SP 800-53 guidelines.
Delegate Internal Responsibilities
The assessment, authorization, and monitoring control family covers evaluation planning and the delegation of team responsibilities. To effectively comply with NIST SP 800-53, organizations must clearly define who is responsible for these actions.
By assigning a specific person or team for implementation, your organization will always have enough resources to ensure compliance is being met.
Additional responsibilities must be delegated to ensure that all newly developed systems are compliant with the publication. Depending on the size of your organization, the same person or team can share multiple responsibilities. But for larger information systems and organizations, you may need to assign several people or teams to handle these varying duties.
Know Your Existing Policies and Operations
NIST SP 800-53 has been revised multiple times since its inception. Each revision makes the guidelines broader so that organizations in different industries can apply the concepts.
In short, NIST SP 800-53 can now be tailored to fit almost any security and privacy needs, regardless of the organization type, size, or industry.
This means that the implementation team must have a deep understanding of the organization’s existing operations and systems. Taking the time to examine and refine those policies will ultimately make it easier to customize these controls to fit the operational needs of your organization.
Use the Control Catalog as Resource
In addition to this compliance checklist, you should be referencing the control catalog as you’re implementing new policies. The latest version of this catalog can be downloaded from the NIST website, and you can find the download link here.
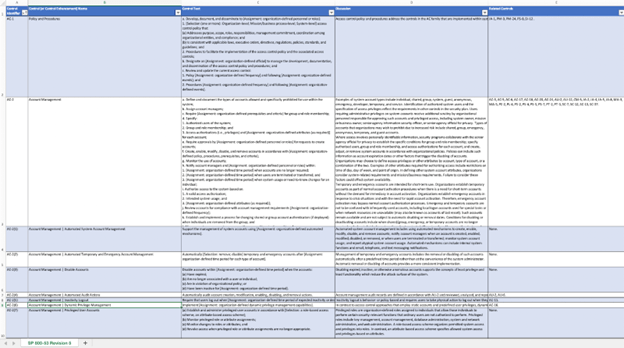
There are nearly 1,200 rows on the spreadsheet. Each row contains the control identifier, the control or enhancement, descriptions, and related controls.
With so much information to dig through, it’s best to come up with a concrete action plan for the catalog. Don’t try to go through this in a single day or week.
Instead, you can create a timeline to go through maybe ten controls per day with your team to get a firm grasp on everything.
Keep Records of Your Implementation
Detailed record keeping is critical for any privacy or security framework. NIST SP 800-53 is no exception.
Someone on your team should be responsible for documenting all steps that you’re taking to achieve compliance. There should be evidence of compliance for every control that you’re applying.
If you ever need to prove your compliance with a third party, having these records to reference will make your life much easier. The recordkeeping process also forces your team to meet compliance standards.
Audit Your Controls on a Regular Basis
The audit and accountability control family is crucial for compliance. It provides all of the recommendations and procedures for logging and auditing.
Follow all of the baseline controls, log storage capacities, and recommended processes for reviews. Audits make it much easier for your team to identify the cause of system issues or breaches. They’re also an excellent accountability solution.
While audits should be scheduled on a regular basis, they should always be done after security incidents.
Apply Common Controls Whenever Possible
Most of the controls in the NIST SP 800-53 can be centrally implemented. That’s because they’re written in a way that’s neutral—applicable to a wide range of systems within the organization.
The publication describes these controls as “inheritable.” This means that other systems can inherit the control from a common control once it’s implemented.
Following the common control approach makes it much easier to roll out controls organization-wide. It also reduces the cost associated with implementation.
For example, let’s say you’re implementing an account access control for users. Some of these controls will be specific to certain systems. But whenever possible, the common approach will save you time and resources.
Identify Sensitive Data
You need to understand where your organization is most vulnerable.
What kind of data does your organization collect? How do you receive that data? Where is that data stored, managed, and how does it get transmitted?
Not all of your sensitive data will always be in one location. It’s common for this type of information to be spread across multiple systems and applications. So don’t make assumptions, and take the time to clearly identify the data and find out exactly where it is.
Categorize Sensitive Data
Identifying sensitive data alone won’t be enough to help you with compliance. You also need to segment that data based on its value and sensitivity.
The easiest way to classify your data is through impact values—low, moderate, or high. Do this for every security objective. Then look at the confidentiality, integrity, and availability of that data.
You can also put the data into different categories based on your organizational goals and business objectives. But the main idea is to categorize everything into simple buckets that can apply all of your sensitive data.
Run a Risk Assessment
An organizational risk assessment is key for NIST SP 800-53 compliance. You need to begin by evaluating your organization’s current cybersecurity risk level.
In simple terms, the risk assessment process should look something like this:
- Identify all possible risks
- Assess the probability of occurrence for each risk
- Determine the potential impact if the risk occurs
- Prioritize risks based on high probability of occurrence and high impact
Once you’ve completed the assessment, you can start working your way through the priority list to remediate serious risks. Then you can assess the effectiveness of your remediation steps.
Provide Effective Personnel Training
The awareness and training control family is the main focus for compliance. It ensures that your team is properly trained on how to use your information systems and how to identify potential threats.
Human error is a top cybersecurity risk. So prioritizing training will help your team understand the different operational risks and privacy threats that they might encounter.
Training should be ongoing and not just provided during the implementation stages.
Keep detailed records of your training policy. You should also invite your team to share feedback about their experience with the training, which will allow your organization to make any necessary adjustments and improve the process.
Manage Access Control
Access control is the first control family. So it’s also a logical place to start implementation if you’re beginning at the top of the catalog.
This initiative starts with establishing rules for who has access to what type of information. Once defined, your access control rules must be strictly enforced.
Some steps in the process involve managing group access and removing stale user accounts. Many organizations apply the least privilege model for access control. This means that users are only granted the minimum amount of access required to complete their jobs.
Check out our complete guide to role-based access control (RBAC) for more information.
Monitor Data and User Behavior
Effective monitoring is a significant part of several different access control families.
This includes AC, CA, IR, and SI—just to name a few. While there are lots of areas you need to monitor for security and privacy purposes, narrowing in on data, file activity, and user behavior is the best place to focus for compliance purposes.
Keep detailed records of how people are accessing your systems and using data. Then you can create a baseline of what’s considered normal activity. Using that baseline, it will be much easier to detect anomalies in data usage and behavior.
For example, you can quickly identify if someone is trying to access data from a different location or if someone is trying to rapidly move massive amounts of data. These types of anomalies can come from malware, system misconfigurations, and insider threats.
Ensure Compliance is an Ongoing Process
NIST SP 800-53 compliance is not a one-off task or initiative. Even after implementation, it’s something that needs to be part of your organization’s DNA.
Having the right team in place to constantly monitor, audit, and keep detailed records will make this easier. Ongoing team training is also key for compliance.
You can refer to this checklist on a quarterly or bi-annual basis as a refresher. Then continue to see if the controls you implemented are still meeting compliance standards.
Refer to the official NIST SP 800-53 publications to see if any new documentation has been released.

