Database Security Best Practices: The Complete Guide
Databases are vulnerable to many threats, including insider threats, human error, Denial of Service (DoS/DDoS) attacks, and malware attacks, to mention a few. We’ve created this comprehensive guide to highlight database security best practices and provide real-world examples of database security at work.
What is Database Security Anyway?
Database security broadly refers to a set of processes, tools, and methodologies implemented to protect and secure a database. Databases face many threats, including insider threats, human error, intrusion, and malicious attacks. Therefore, database security is concerned with protecting the integrity of the data inside the database.
Furthermore, these security measures attempt to secure all other aspects of a database, including:
- Database workflow applications
- The database server
- Database management system (DBMS)
Robust database security is essential for several reasons. First, a database leak or breach, whether accidental or malicious, can have far-reaching effects. The potential consequences of such a breach may include financial loss, intellectual property loss, brand reputation damage, and penalties and fines.
Databases are attractive to threat actors for the simple reason that they contain valuable data such as customer information. Cybercriminals can sell sensitive business information to third parties or use it as leverage to extract a ransom.
Below are a few real-life data security examples to give us a better understanding of the topic.
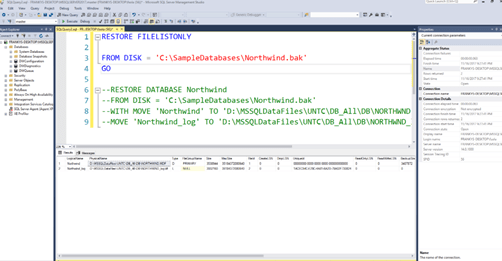
Example #1 – SQL Slammer Worm Targeting Unpatched Microsoft SQL Servers
SQL Slammer was arguably the most significant IT security event of 2003. The SQL Slammer was a worm targeting unpatched Microsoft SQL servers, causing what some may call a technological apocalypse. South Korea, where the worm is suspected of having originated, saw interrupted cell phone and internet coverage of up to 27 million people. In addition, the worm infected more than a quarter of a million computers worldwide within the first weekend of its appearance.
Similarly, The Bank of America had its 13,000 ATMs temporarily knocked offline in the US by this worm. The worm exploited a known buffer overflow flaw in MS SQL Server and used UDP port 1434 to target vulnerable servers visible on a network. The breach caused various issues, including network sluggishness and taking down databases within minutes of infection. However, this MS SQL Server flaw had already been identified and patches created. Therefore, only unpatched servers were vulnerable to the attack.
The worm was only 376 bytes of code but still proved catastrophic. It replicated quickly and identified new targets to infect once it found its way into the server. Mercifully, the worm was easily removed since it didn’t write itself directly onto the disk. The worm also didn’t take control of infected machines further dampening its potential impact.
This incident demonstrates the importance of updating database management software, an industry best practice. This attack could have been entirely avoided if organizations had stayed up-to-date with installing security patches and fixes.
Example #2 – The Human Error Factor in Database Security
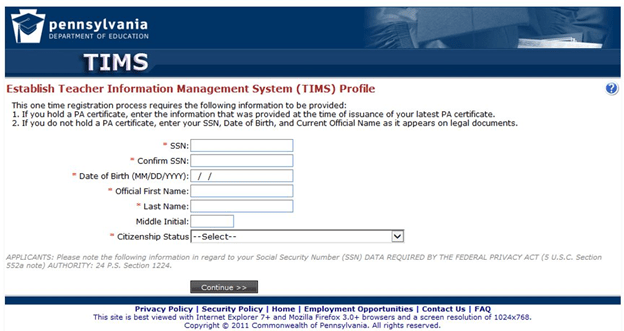
Not all database breaches are malicious or intentional. Sometimes employees can unwittingly leak sensitive data, as demonstrated in the Pennsylvania Department of Education in 2018.
The Department of Education uses the Teacher Information Management System (TIMS), an online platform for teachers and administrators. Educators can collate their education certifications and manage their profiles on the platform. Similarly, administrators can use the system to review applications and credentials.
The breach resulted from human error on the part of an unnamed employee in the governor’s Office of Administration. It only lasted thirty minutes. But during this time, anyone accessing the TIMS portal could view teachers’ personal information, including full names and social security numbers.
The system was taken offline while experts attempted to resolve the breach. It remained unavailable for at least a week, inconveniencing users and prompting complaints to the education department. The breach did not have any severe consequences besides the inconvenience.
This incident could have had a worse ending if the sensitive information had gotten into the wrong hands. Regardless, this case highlights the importance of access control and giving users the minimum permissions necessary to do their job.
Example #3 – Insider Threats to Database Security
Outsider threats and human error are database security concerns. However, some data breaches happen internally. They are perpetrated by malicious employees. Worse, these employees know the organization well. Plus, they have access to computers and databases. A well-executed internal database breach can be catastrophic.
Elliott Greenleaf, a St. Louis based law firm, is a perfect demonstration of the role of insider threat to database security. According to court papers, four former attorneys planned to exit the law firm for a competing firm for months. However, the employees copied and destroyed sensitive corporate data before leaving the firm.
The attorneys allegedly copied and destroyed files on clients, records, correspondence, and property. This data loss effectively made the firm unable to retain its clients. Again, this example emphasizes the importance of securing databases against all potential threats, including from current and former employees.
How to Get Started With Database Security Best Practices
We can now fully appreciate the importance of database security. Below are a few steps you can take to bolster your database security in the short and long term.
Step 1 – Secure Your Physical Database
It is easy to overlook your physical database, so this is an excellent place to start. This is for organizations that still use physical servers or have a hybrid network of physical and virtual servers. These servers are vulnerable to physical attacks, so you need to take appropriate measures to secure them.
Some of the security measures to consider implementing include:
- Using controlled doors – Controlled doors help you implement access control. This way, you know exactly who accessed your servers and when. In addition, things like keycards, RFID tags, passwords, and biometrics help keep a tight reign of employees who can access the physical servers.
- Setting up video surveillance – This measure will help you maintain a visual record of everyone accessing the server room. This is critical in case an unauthorized person can bypass biometric identification. These cameras will also let you see what people are doing inside the server room.
- Using locking kits to protect server hard disk – Admittedly, it is difficult to make off with a physical server undetected. However, someone may open up the server and retrieve the hard disk. Locking kits can make it difficult or impossible to access the hard disk without a specialty tool. In addition, the extra effort needed to access the hard disk may provide deterrence.
- Keeping backups separate from the server – It may sound like a no-brainer, but it is a good idea to keep your server and backups separate. Backup disks and hard drives are easier to conceal and transport than physical servers. So keeping them in the server room makes it easier for people who might want to access your database.
Virtual server users aren’t left out. You can boost database security before you even choose a hosting company. Typically, you may want to stay away from free hosting services. These options usually don’t implement stringent security measures. Lastly, investigate your hosting company’s previous data loss incidents and the security measures it puts in place to prevent data loss.
Step 2 – Isolate Your Database Servers
It may be easier to host your database, websites, and apps on the same server. However, this practice undermines database security. It is much easier to implement database security controls on an isolated server. For instance, you can easily use a security information and event monitoring (SIEM) tool on an isolated database server. This will allow you to get instant information about your database security posture and spot potential breaches in real-time.
Additionally, using a shared server introduces additional attack vectors to your database. For instance, web servers are located in a publicly accessible DMZ and, therefore, low-hanging fruit for cybercriminals. In this instance, someone hacking your ecommerce platform gets access to sensitive customer payment information. The hacker would only access your organization’s external-facing services with an isolated database server.
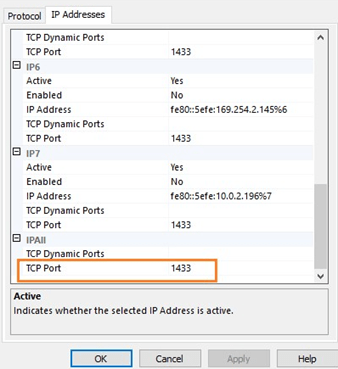
Also, be sure to turn on all the security controls and protocols that your database server offers. Similarly, configure the server in ways that boost security. For example, you can start with assigning a new network port, preferably one that isn’t used for other services. Hackers typically rely on default ports since they are already well known.
You should also disable any server features, applications, and services you don’t need or aren’t using. This action will help to minimize the database attack surface. Ideally, you should only have the data components required for the database to perform its tasks. This strategy also helps improve performance by limiting resource utilization. Likewise, it will make administration easier by minimizing managed components and services.
Finally, use firewalls to control traffic between your database and website server. Ideally, the firewall should only allow traffic from pre-approved web servers and applications. The server should also limit outbound connections to only the necessary ones.
Step 3 – Control Who Has Access to the Database
Generally, you want the least number of people gaining access to a database. In an ideal world, you’d grant the bare minimum permissions an employee needs to do their job. This is known as the principle of least privilege. Additionally, the employee would only have database access for the duration of the tasks.
For example, you can assign an employee the processadmin and serveradmin roles if their only job is to end processes and shut down the server. If practical, the employee might also need to request this permission from the system administrator every time they need to perform this action.
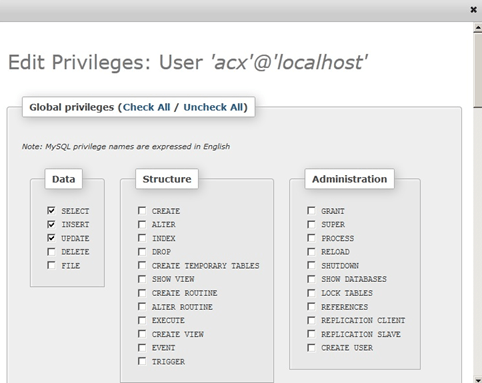
A systemadmin role would allow them to perform any action on the server, including configuring the server settings. The latter example violates the principle of least privilege.
However, there are different ways to approach database access management, depending on your organization’s size.
Smaller organizations may opt to grant permissions based on roles or groups rather than giving permissions directly to employees. User groups and roles are perfect for this purpose. You can create containers with groups and roles and assign them the relevant permissions. Then you can give employees and new hires to the suitable group or role. This strategy simplifies permission management.
Larger organizations may benefit from access management software to automate authorizations. In this case, authorized users get a one-time temporary password together with the specific privileges they require to do their job. The software also logs everything the authorized users do while inside the database.
Other database identity and access management best practices to consider implementing include:
- Implementing zero-trust security
- Using multi-factor authentication
- Minimizing or avoiding privileged accounts
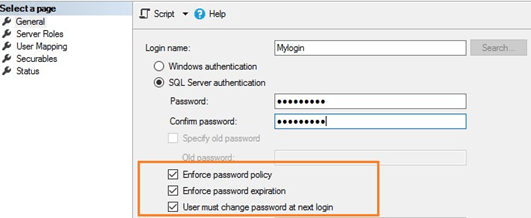
- Enforcing a strong password policy
- Conducting routine identity, access, and user privileges audits
Step 4 – Stay Current with Patch Updates
Many organizations use third-party management tools to complement inbuilt database tools. These widgets and plugins may help to enhance synchronization, collaboration, security, visual rendering, data editing, and much more.
However, these third-party tools also increase the databases’ attack surface. For instance, hackers may use vulnerable or outdated plugins or widgets to access your database. For this reason, third-party tools often release regular updates to improve security and performance. So be sure to update your third-party tools as soon as the new patches become available.
Similarly, update your database management software and applications and operating system regularly. For example, Microsoft periodically releases SQL Server updates. Enabling automatic updates ensures that your system is current.
However, larger organizations may need to test the updates in a test environment before implementing them. The reason is some updates, such as Hotfixes, aren’t rigorously tested since they are designed to be quick fixes for pressing customer problems.
Step 5 – Constantly Test Your Database Security
You’ll need a way to check if the database security measures you’ve implemented so far work. The main thing here is to find vulnerabilities in your database before hackers do. So you’ll need to think and act like a cybercriminal to identify weak points in your database security protocols.
To this end, you can use penetration testing tools together with vulnerability testing tools. These tools allow you to hack your database and are great for identifying loopholes and flaws in your security posture. In addition, you can use the results of these tests to bolster your database security further.
Lastly, monitor your regular database workloads and use this information to establish a baseline. This way, you can immediately tell when there is a significant shift from the usual database activity. This shift may indicate a potential breach, so launch a security investigation as soon as possible.

