Best Vulnerability Scanning Tools of 2022
The best vulnerability scanning tools can identify and report known vulnerabilities in your organization’s IT structure. Using these tools gives a fair idea of the underlying security threats in systems by providing insights into potential security weaknesses.
If you’re looking to implement network vulnerability scanning as a fundamental part of your system‘s cybersecurity, you are in the right place. In this guide, we’ll discuss five of the best vulnerability scanning tools available on the market, along with a step-by-step rundown to help you select the right software for your organization.
Nessus Professional
Providing exceptional vulnerability assessment, Tenable’s Nessus is a remote security scanning tool that can easily scan computer systems, identify vulnerabilities in your IT structure, and report the detected vulnerabilities to your team.
Nessus is designed to make vulnerability assessment intuitive and straightforward. Its developers take pride in providing security practitioners with a solution built by security professionals.
Once implemented, Nessus can perform point-in-time assessments to help security professionals spot and fix vulnerabilities, including malware, software flaws, misconfigurations, and missing patches. What’s more, it can do this across a variety of operating systems, devices, and applications.
Additional features include customizable reporting, access to pre-built policies and templates for auditing and patching purposes, and real-time updates.
That said, we recommend this vulnerability scanning tool for more experienced security teams as its interface has a slight learning curve. But if your team can manage it, it’s a great option and can be used alongside penetration testing tools to target and exploit potential weaknesses.
Pros
- Provides a wide range of configurations
- Has predefined testing modules
- Classifies vulnerabilities into risk-based categories
- Regularly updated for new CVEs and features
Cons
- Complex graphical user interface
- Scans take longer to complete
- Plugins inside plugin groups cannot be disabled
Pricing
Pricing starts at $2,990 for the first year. It increases to $3,390 if you opt for advanced support.
A seven-day free trial is also available.
OpenVAS Vulnerability Scanner
As the name suggests, OpenVAS is a free open-source tool that helps IT departments scan their servers and network devices to identify, analyze, and manage vulnerabilities.
It scans through open ports, misconfigurations, and vulnerabilities in existing facilities to look for an IP address and check for any open service. After the scanning is complete, you’ll receive an automated report in your email for further study and system rectification.
The tool can be paired with a graphical user interface (GUI) to allow effective reporting in managing technological risks. Custom configuration lets you set up the tool in line with your own requirements and preferences. Being open-source, anyone can contribute to the tool, which considerably boosts its security.
OpenVAS has a common vulnerabilities and exposures (CVE) coverage of around 50,000, which it uses to search and test vulnerabilities and bugs in the underlying infrastructure. But the CVE coverage is still limited compared to other vulnerability scanning tools.
You can operate the scanning tool from an external server. This makes it easier to identify any exposed ports or services and promptly eliminate threats.
Pros
- Free forever
- Greater flexibility—you can plan tasks on a daily, monthly, or yearly basis
- Comprehensive vulnerability scanning and vulnerability management
- Offers detailed documentation and tutorials
Cons
- Plugins aren’t updated frequently, which makes scanning slower
- Requires frequent maintenance
- Tends to report false positives at times
Pricing
OpenVAS is free to use.
IBM Security QRadar
IBM Security QRadar is another powerful vulnerability scanning tool that helps IT teams detect, assess, and prioritize threats.
It correlates information from its security scans with network topology and connection data, after which it manages risk using a policy engine, complete with automated compliance checks. This makes the whole process of vulnerability scanning effective and accurate.
Once a credible threat is identified, IBM Security QRadar performs AI-powered investigations that can give you access to intelligent insights into the root cause and scope of the threat. Using this information, you can prepare your first-line security analysts and accelerate security operations processes to reduce the impact of incidents.
Another advantage of IBM Security QRadar is its advanced analytics. It helps prevent security breaches, prioritize and perform remediation, and maintain regulatory compliance.
An intuitive dashboard gives you a single view of all of this information at once.
Pros
- Versatile—suits SMBs and large organizations alike
- Tons of capability options
- All in one solution that can be used as a logo, collector, and processor in a limited environment
- Automates threat detection and also prioritizes them for further investigation
Cons
- Steep price tag
- Lacks a live chatbot
- Software updates can cause log interruption for a short time
Pricing
IBM Security QRadar offers two plans: a free Community Edition and a Cloud Standard Edition that starts at $800 a month.
A free 14-day trial is also available.
Acunetix by Invicti
Acunetix is a fully automated web vulnerability scanner that easily identifies and sends alerts on over 4,500 web application vulnerabilities, including common SQL Injection and XSS.
Advanced vulnerability management features are fitted right into Acunetix’s core, helping it prioritize risks based on data through a single, consolidated view and integrate the scanner’s results into other platforms and tools. It’s one of the best at scanning WordPress, so if you have heavy WordPress deployment, this is the vulnerability scanning you need.
The DAST + IAST scanning and intelligent crawling technology make sure every application has been crawled comprehensively. Integrating into other development tools is also possible to ensure a seamless work process between your security team and developers.
What’s more, the Acunetix crawler fully supports HTML5 and JavaScript, as well as Single-Page applications. This makes it more efficient to audit complex, authenticated applications. By providing comprehensive results and fast scanning, complete with intelligent automation, Acunetix can help your organization reduce risk across all types of applications.
Pros
- Pleasant and user-friendly GUI
- Threat prioritization and classification features help resolve issues based on your organization’s preferences
- Easy to set up assessment procedure
- Prompt customer support
Cons
- Limited scanning options
- Pricing changes often
- Clunky target license model
Pricing
Acunetix doesn’t provide pricing details on its website, so you’ll have to request a customized quote.
Rapid7 InsightVM
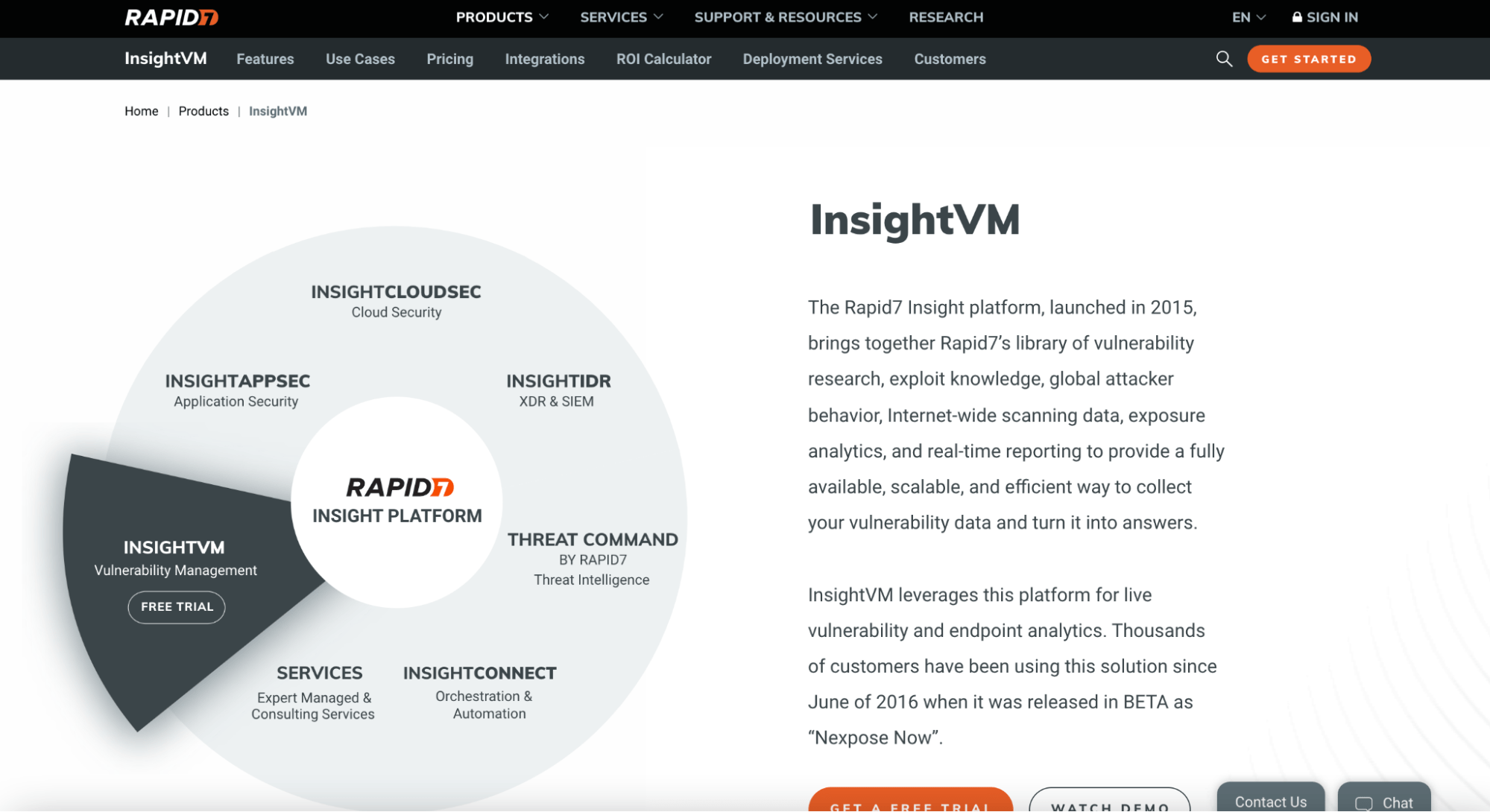
InsightVM is a top-rated, open-source vulnerability manager that put its developer, Rapid7, on the global map.
InsightVM scans all new devices connected to your network to provide real-time vulnerability identification. It can automatically assess virtual, physical, and cloud infrastructures, as well as provide solution-based remediation and risk scoring and prioritization facilities.
What’s more, you can watch all the information on live, interactive dashboards to stay on top of your security systems.
Typically, most vulnerability scanners categorize risks using a high, medium, or low scale. InsightVM takes a different approach—it considers the age of the vulnerability (example: which malware kit is used in it) and fixes the issue based on its priority.
The versatility of this tool can give IT admins a serious advantage. InsightVM can be incorporated into a Metasploit framework, which boosts the tool’s efficiency of detecting and scanning devices the very moment any new device accessed your network.
Thanks to its tracking and monitoring abilities, you can take a more proactive approach with InsightVM to create accountability and recognize progress.
Pros
- User-friendly and intuitive
- Performs deeper vulnerability scans of all assets with an IP address in your network
- Top-notch reporting and automation capabilities
- Offers useful integrations
Cons
- Dashboards can be confusing at times
- Setup is a little clunky
- Complex filters make granular and advanced searches and reporting difficult
Pricing
InsightVM charges users based on the number of assets, and the more assets you buy the less you spend in total. For example, if you decide to pay for 500 assets, you’ll pay $22.08 yearly, but for 1000 assets, you’ll only pay $19.56 yearly.
How to Pick Your Vulnerability Scanning Tool
Not all vulnerability scanning tools are created equal. That’s why we created this step-by-step guide to help you choose the most suitable option for your system.
Let’s take a quick look.
Step 1: Know Your PCI DSS Vulnerability Requirements
PCI DSS requires organizations to do quarterly internal and external vulnerability scans. In addition to this, performing scans right after you change or update any equipment or software is also recommended.
That’s why it makes sense to look for vulnerability scanning tools that offer unlimited scans per target to minimize the overall cost.
Next, you want a tool that fulfills the basic requirements set up by PCI DSS. This is particularly important if your organization deals with confidential and sensitive information. Luckily, some scanning tools go beyond the basic requirements. Find out if your prospective tool can take care of issues not explicitly stated in PCI requirements.
If yes, move on to Step 2.
Step 2: Find Out How Many False Positives The Scanning Tool Reports
False positives refer to a situation when a vulnerability scanning tool detects a vulnerability when it doesn’t exist (hence the name “false”). A common reason for this is when a bug has been patched up but still shows up as a vulnerability on the scan.
False positives lead to wasted time and create unnecessary chaos. When considering options, find out how many false positives the tool typically reports. The higher the number of false positives, the more time you’ll lose sifting through issues. Only consider vulnerability scanning tools that ensure zero false positives—or have very few of them.
You’ll also find options that let you request false-positive checks.
Step 3: Ensure Compatibility With Your Organization‘s Unique Needs
The next thing on your to-do list is to check for compatibility. Your prospective vulnerability scanning tool should be able to adjust to your company‘s unique requirements, goals, and staff expertise.
The tool’s signature database should cover all of the major operating systems, infrastructure components, and apps to integrate with your existing systems. Compatibility with your legacy systems is also important for a smooth transition as some employees may show reluctance at the beginning.
Step 4: Dive Deep Into the Prospective Tool’s Scanning Process
This is the last stage where you ask questions—a lot of them—to determine how well the prospective vulnerability scanning tool meets your requirements. Below, we’ve listed these questions into different categories:
- Updates: What does the update process look like? Is the scanner updated every day, every week, every month, or every year?
- Plugins: Is the internal scanner compatible with correctly updated plugins?
- Vulnerability Scanning Capacity: How many vulnerabilities can the scanning tool search for? Skip tools that offer anything less than 50,000.
- Reporting Capabilities: How does the reporting look to you? Do the reports give clear and accurate recommendations to effectively patch vulnerabilities and bugs?
- Size: Can the tool overload and crash vulnerable servers?
- Customer Support: Do the developers provide technical assistance to help you fix vulnerabilities? Will you have to pay extra for this support?
- Trial period: Does the tool offer a trial to let you test-drive features before making a final commitment?
All the above are important considerations, and your priority is to look for tools that meet all of your requirements.

