How to Secure Your Business’s Social Media Accounts
Social media isn’t just a “big brand thing” anymore. It has become an indispensable part of any business’s success and survival, regardless of its size.
Facebook, Instagram, Twitter, and YouTube have now gone beyond their initial purpose of entertainment and communication and have established themselves as valid advertising tools to enhance promotional and marketing activities.
No doubt social media accounts are powerful tools. But when in the wrong hands, they can also become a nightmare.
If you think your business is safe, we have news for you: it isn’t.
Cybercriminals are taking over business accounts to steal personal information, post basic spam, or draw attention to global issues or personal agendas. Getting hacked can be a major blow to your business’s reputation.
Understandably, nobody wants to be the next victim. It’s why we created a step-by-step guide below to help you secure your business’s social media account and enforce a security-first approach.
Step 1: Educate Your Employees in Social Media Security
Your employees are your greatest assets, which is why the first step towards securing your business social media accounts begins with their education and training.
This makes sense considering you have to trust employees with tons of responsibility to maximize returns from social media. And while your social media team and IT department may already know the ins and outs of the platforms and how to use them securely, other employees won’t.
Familiarize your employees with social media and train them in security best practices. The good news is you’ll find many structured social media training programs your employees can take to learn social media network best practices while maintaining secure control.
What’s more, these programs will also make them better at their jobs, improving the overall performance of the social media campaigns. Just be sure to select training programs that go beyond basic education and cover advanced themes like social media etiquette and creating online brand awareness.
While you’re at it, make sure they also know the importance of clicking with caution. Spammy and virus-infected links are a common way for phishers and malicious agents to gain entry to your network and unleash chaos.
Step 2: Have Secure Login Credentials
Having strong, secure, and backed-up account login information when creating social media accounts is a no-brainer.
Your passwords especially have to be strong for all your social media accounts. If it isn’t, you are practically begging to be hacked. Here are a few guidelines to keep in mind when creating your social media passwords:
- Ensure they are 12-16 characters long
- Make them a random combination of upper and lowercase letters, symbols, numbers, and punctuation marks
- Avoid using easy-to-guess names like the company name, dates of birth, zip code, office location, and so on
- Have different passwords for different social media accounts
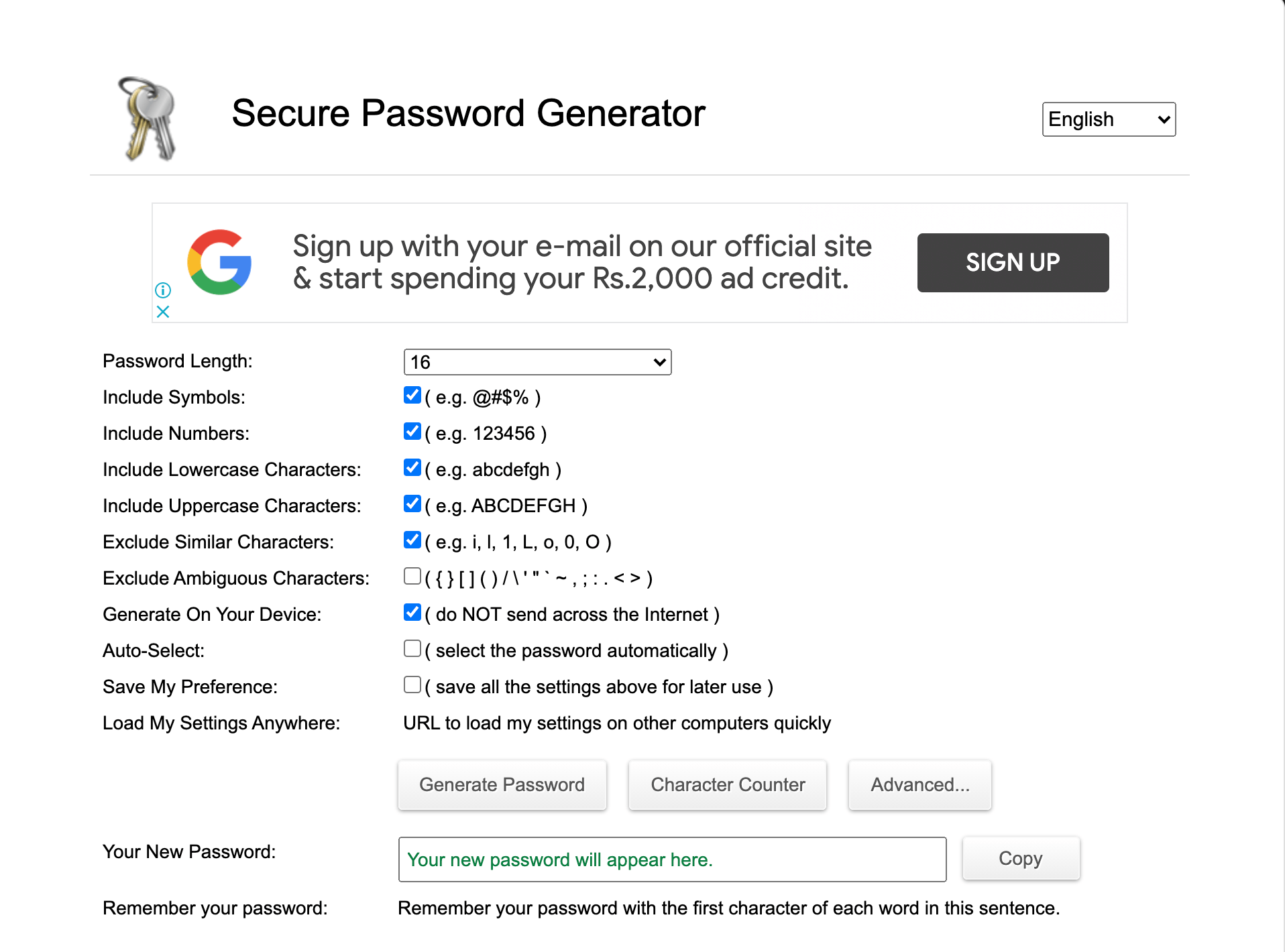
We also recommend using a password generator like PasswordGenerator.net that randomly creates strong and secure passwords.
You should also change your passwords regularly to prevent security breaches. Although this is a complex process, it’s necessary to protect your social media accounts from unauthorized activity.
Next, store all your business’s social media account login information in a secure place and away from the public eye. While you can backup your records on an external hard drive or USB, we don’t recommend it. Instead, create a password-protected computer folder and store it there. It’s much safer.
Step 3: Centralize Social Media Channels
Your team has to manage multiple social media accounts to create a solid online presence, which also involves giving employees more power as you scale. Unsurprisingly, maintaining control of so many accounts across several different platforms can be difficult.
Keeping this in mind, you can consider bringing all your social media accounts under central control.
Do an audit of all your social media accounts within your enterprise, taking note of who manages what. You should also know which employee has access to the different accounts. Remove any extra or obsolete social accounts and rescind access permissions from anyone who shouldn’t have it.
The easiest way to centralize control is through consolidating accounts within a social media management system. These systems allow you to draft messages and publish them on various accounts from a single interface while simultaneously letting you monitor all social messaging and activity.
Moreover, social media management systems come equipped with additional security features, such as built-in malware and spam tools, which further enhance your account safety.
Step 4: Enable Two-Factor Authentication
For those of you who aren’t aware, enabling two-factor authentication is an excellent security measure that confirms the user’s identity by using a combination of two different components.
These are generally an account password and a confirmation code, which is sent to the user either via email or text message. This is a super effective and easiest way to prevent hacking attacks, and therefore, totally worth the extra hassle to ensure your account for security.
Step 5: Secure Your Business Equipment
You can’t secure your business’s social media accounts if your devices remain unprotected.
The first step is to install strong antivirus software on all your office computers to prevent cybercriminals and viruses from getting access to your account or any other business information for that matter. There are many amazing software programs, such as Norton and BullGuard, that auto-scan your computer periodically, so you don’t have to worry about doing it manually.
Next, block access to dangerous sites or sites known to have viruses on them. You’ll be surprised how effective limiting site access can be, whether it’s a sketchy video streaming site or a free music download site, to secure your office computers.
Step 6: Use Private WiFi Networks
It’s always better to use a private WiFi network, regardless of whether you manage your business social media accounts or do any other company work in general. The thing about private WiFi systems is they are always password-protected, giving them that extra layer of security to keep cybercriminals at bay.
Most small business founders make the mistake of using public WiFi to save a few bucks. What they don’t understand is the endless list of dangers associated with using public WiFi.
Many cybercriminals have created fake WiFi networks in the past to steal user information. What makes it worse is that they do it really cleverly to avoid suspicion.
For instance, a cybercriminal may create a public WiFi network called “Starbucks Guest“ and make it available near a Starbucks café. Most customers won’t second guess that it’s a fake WiFi connection because of the brand name in the title. As soon as customers join this network, the threat actor will get access to all their information and work.
In addition to this, public WiFi networks may also expose your computer to malware and viruses. Yes, installing antivirus software can be helpful, but switching to a private WiFi network is undoubtedly the best option.
Step 7: Prepare for the Worst
When it comes to network security, nothing is guaranteed. There always is a chance, no matter how slim, for cybercriminals to gain access to your social media account.
An employee might miss a critical error, a button can be clicked by mistake, or a malicious agent might find backdoor access into your account.
You must have a crisis plan in place to cover the circumstances where something goes wrong.
Employees should be trained on how to respond quickly and effectively. Having a contingency plan that outlines testing and evaluation guidelines can also be useful to control the damage.
Keep in mind that social media happens in real-time. This also means your response to any unauthorized entry or a hacking attempt will happen in real-time as well.
We highly recommend using social media management tools that allow you to oversee all communication at once. They will immediately alert you in case of a potentially harmful situation or odd activity on your accounts.
Common Problems When Securing Your Business‘s Social Media Accounts
Learning how to secure your business’s social media accounts involves trial and error. You’ll find yourself getting stuck at times or coming up with even better suggestions based on your employees’ skills and technology availability.
To set you for network security success, we’ll discuss the main stumbling blocks people face when securing their social media accounts.
Problem 1: Social Media Oversharing
Human beings are social people, and considering the whole point of having social media is to be social, we aren’t always careful about what we end up sharing on our accounts.
For example, posting about the company’s annual picnic and showing employees having fun may look great for social proof. But it’s also a very public announcement to your social audience that your office is abandoned. This is essentially an open invitation to thieves to come and steal information and equipment from your office.
Unfortunately, this is just one of the many ways in which we end up unintentionally compromising our company’s security.
The best way to avoid this is to train employees to have a security-focused mindset and be mindful about what they share. You can also require all employee posts to be screened by more than one person before they go live for extra measures.
Problem 2: Clicking on Suspicious Links
We’ve already discussed how employees often end up clicking on suspicious links, which leaves your network and social media exposed to malicious agents. But sometimes, employees still get tempted and forget that not every link on social media platforms is safe.
Suspicious links can lead to malware and viruses or even give direct access to cybercriminals to your information. These are generally clickbait wording and content, sweepstakes and contest links from unverified accounts, quizzes on popular topics or TV shows, and so on.
The only way to avoid this is to make employees more cautious before clicking on social media or emailing. Encourage them to always take a second look, and if they have any suspicion, avoid clicking on the link.
Problem 3: Working With Third-Party Applications
Third-party applications require you to give them access to your social media accounts, and we often end up granting this without giving a second thought.
Cybercriminals are well aware of this, which is why they are using these apps to manipulate you. The only way to avoid becoming a victim is to be selective with the third-party applications you use and grant access to only legitimate ones. Additionally, you should read the details of the kind of access you’re authorizing to the particular application to be safe.
Some applications only need minimum permissions, such as having the ability to read and post content, which is a good sign. However, some applications may want access to your more private details, which is why you must read the fine print before approving any request.
You should also log in to all your social media accounts to cross-check what applications already have access to your profile. Remove any application that you feel looks shady.

