Cyber Security Training for Employees: The Ultimate Manual
Most people associate cybersecurity threats with brute force attacks by faceless hackers. But, according to a Cybint report, 95% of successful cybersecurity breaches can be attributed to human error. Therefore, cybersecurity training for employees is indispensable for changing user behavior and minimizing potential vulnerabilities that hackers can exploit.
What Is Cybersecurity Training Anyway?
Employees that don’t understand common cybersecurity threats may take actions that expose the company’s network to cybercriminals. Similarly, employees must understand their role and responsibility for protecting systems and data.
Cybersecurity training is a type of formal training program designed to equip the workforce with the necessary knowledge to identify, report, and manage common security threats.
This training equips workers with a holistic understanding of IT security issues and how to limit security breaches. Ideally, employees learn how to:
- Identify security issues.
- Limit the chances of hackers gaining access to personal information and accounts.
- Protect sensitive company data.
- Respond to cybersecurity issues.
In short, cybersecurity training attempts to solve human error problems, such as neglecting to use a strong password or unwittingly downloading malware-infected attachments. It also trains employees to know how to adapt in case a cyberattack or security issue occurs.
How Cybersecurity Training for Employees Works
As we’ve already seen, human error is the leading cause of cybersecurity breaches. It is crucial to understand how employee actions may expose the company’s data or system to cybersecurity incidents.
We can broadly categorize human error into two groups:
Skill-based human error is when an employee makes a mistake when performing a familiar task. This mistake may result from a temporary lapse in judgment, distraction, negligence, or fatigue. For example, a worker may email sensitive company information or data to the wrong person by accident.
The decision-based human error refers to when a user simply doesn’t have the proper knowledge to avoid cybersecurity incidents. In this case, the worker is unaware that they are making a mistake in the first place. For example, an intern may be clueless that they shouldn’t use their work email password for other services. It makes sense to use one password for all subscriptions in the intern’s mind since it’s easier to remember.
Both types of human error pose serious data security concerns. As a result, cybersecurity training is concerned with reducing or even eliminating instances of human error that may put the company’s data and systems at risk.
Below are two real-world examples relating to cybersecurity training for employees.
Example 1: NHS Trust HIV Status Leak
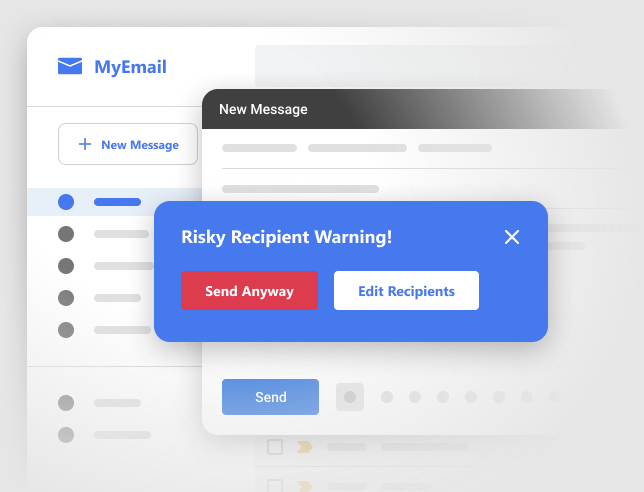
Misdirected email is one of the most common causes of data breaches. According to an Egress report, misdirected emails are the third most common cybersecurity threat behind hacking and malware. According to the same report, 44% of executives believe that employees have accidentally exposed sensitive information, including personally identifiable information (PII).
A misdirected email refers to an email sent to the wrong person or address.
56 Dean Street, a sexual health clinic, was the victim of a misdirected email that revealed the HIV information of 781 people in September 2015. The names belonged to individuals who had opted into the HIV clinic’s online service. Worse still, the incident happened in a small town where there was a high possibility of people recognizing each other’s names.
The error occurred when a pharmacist entered emails in the “to” field instead of the “bcc” field. As a result, the email, intended to be an HIV treatment questionnaire, was sent out as a group email instead of blind-copying the recipients.
Information Commissioner, Christopher Graham, commented on the matter, terming the error a “serious breach of the law.” The affected individuals were understandably upset. As a result, the Information Commissioner’s Office (ICO) fined the NHS trust £180,000. The Trust’s Medical Director, Zoe Penn, issued an apology and accepted the ICO ruling.
Comprehensive cybersecurity training for employees covers misdirected emails. Without commenting on the trust’s security protocols, it is possible to point out that such training might have prevented the unintended breach.
The training may involve explaining why misdirected emails are a serious concern. The employees may also be trained to check every attachment and email address before hitting the send button, using an email checking software, or adding a send delay.
Example #2: WannaCry Ransomware Attack
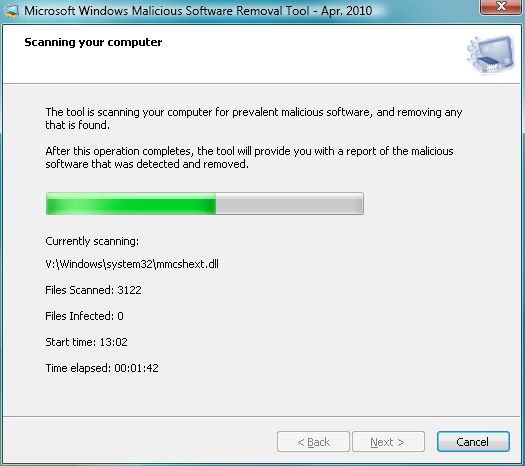
The infamous WannaCry ransomware attack of May 2017 is another excellent example of the importance of cybersecurity training. The ransomware infected more than 230,000 computers. The UK’s National Health Service (NHS) was arguably the most notable attack victim. The malware rendered NHS equipment and systems inoperable, including critical equipment like MRI machines.
Investigators later credited The Lazarus Group, a North Korean collective, for the attack. The ransomware specifically targeted a vulnerability in older Windows systems. In addition, the self-perpetuating malware used infected devices as a delivery system and could spread through a network exponentially.
The worst part is this attack was utterly avoidable. Microsoft had released a patch update for this specific vulnerability just two months before. Blocking the malware was as easy as downloading the patch. Unfortunately, the malware resulted in billions of dollars worth of damage.
Furthermore, Windows 10 systems provided automatic updates for this patch. Unfortunately, the update also didn’t support older Windows version XP. Although the company eventually released a patch for the legacy OS, it was too late for many computers connected to the internet.
This incident highlights the importance of updating software and operating systems regularly. In addition, comprehensive cybersecurity training emphasizes the importance of updating systems and devices. For example, the NHS was an easy target for using older computers and operating systems.
How to Get Started With Cybersecurity Training for Your Employees
It is impossible to overstate the importance of training employees on cybersecurity. But this is a broad topic, so getting started implementing the program can be a challenge. Below are a few crucial steps to lead you toward an effective training program.
Remember that everyone who uses a computer at the organization should be part of the training.
Step 1: Get Buy-in From Senior Management
Employee training is expensive and resource-intensive. And, there is probably a backlog of potential training programs to improve any number of things, including efficiency, skills, and competence. However, data security should be a priority, and it is essential to communicate this urgency to senior management.

It is also important to remember that cybersecurity training has far-reaching consequences beyond the course. For example, the program will likely change your company policies, processes, and culture. Getting executive buy-in will also help minimize employee resistance to new ways of doing things.
The best way to get senior management on your side is to outline the ROI the training has to offer. You can start with an inventory of all the data the company collects and stores. Then, it is easy to convince stakeholders of what is at stake in case of a breach.
Similarly, data security training can help with compliance. Be sure to reference regulations relating to your industry, such as General Data Protection Regulation (GDRP), Personal Information Protection and Electronic Documents Act (PIPEDA), or California Consumer Privacy Act (CCPA) regulations. Many of these regulations require formal employee training. For example, HIPPA mandates that covered entities must implement a security awareness and training for all workforce members, including management.
Finally, develop some metrics to explain how you intend to measure the training program’s success. These metrics may include phishing simulator metrics, quiz or test results, or overall risk rating.
Step 2: Decide How You’ll Deliver the Training
There is no such thing as a one-size-fits-all training program. Instead, there are multiple ways to deliver the training. Deciding how to provide the training will inform the details of the program who, what, where, and how. Each delivery method Lalso has its distinct advantages and disadvantages.
Your options here include:
- Conventional delivery – This option is perhaps the easiest to implement. It involves handing out electronic or paper-based materials on cybersecurity. However, there’s the risk that employees may not comprehend or even read the material.
- Online delivery – This training method relies on multimedia platforms such as interactive meetings, emails, or chat sessions. Online delivery may be more interesting for participants compared to conventional delivery. There are even free online training programs that cover cybersecurity fundamentals satisfactorily. However, it can be challenging to measure the success of these online training programs. Online programs may also be too broad to cover your organization’s specific needs.
- Instructor-led delivery – This option is a step up from online programs in terms of effectiveness. A security expert takes charge of the training, usually via formal presentations. Instructor-led delivery supports real-time questions and answers and can be customized to meet your organization’s needs. However, there are downsides to instructor-led delivery. For example, the concepts may appear too abstract to employees. The delivery method can also be expensive, and employee engagement can be challenging.
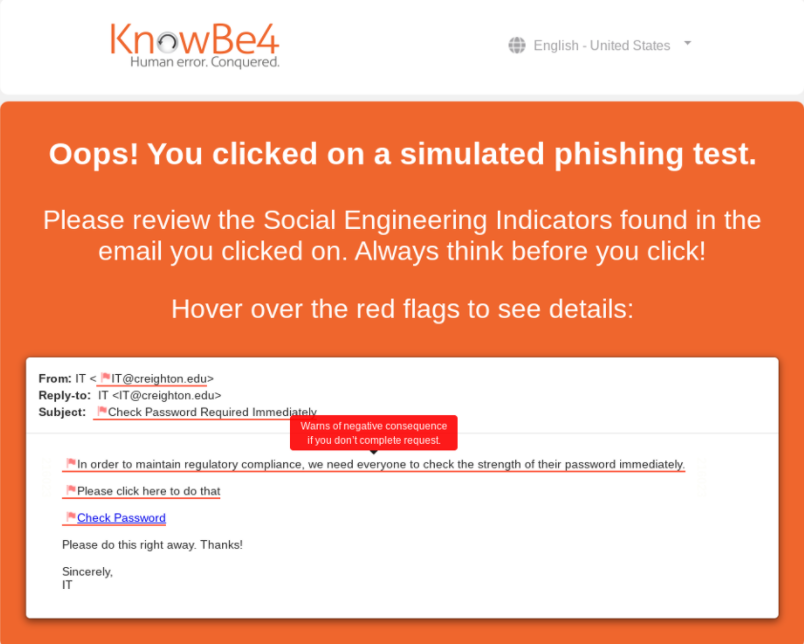
- Simulation-based delivery – This training program is perhaps the most practical option for participants’ engagement. Here, employees are presented with security threats in a simulated environment and training material. The students must actively participate in simulated scenarios, such as a computer-generated phishing attack. You can easily track metrics, such as how many people clicked on the fake phish. However, these programs can be expensive and difficult to identify and implement.
Step 3: Identify What to Include in the Training Program
Again, there is no standard template for precisely what you should include in your training program. Practical training depends on a variety of factors, such as your industry. For example, a business that processes a client’s payments may have different training needs than a healthcare company that stores patients’ medical information.
However, there are certain commonalities among effective security awareness training. At the very least, your training program should include most or all of the following topics:
Passwords
According to a report by the Hosting Tribunal, compromised passwords account for 61% of data breaches. Experts agree that weak passwords are the most common entry point for cybercriminals, so it’s an obvious place to start.

Unfortunately, many people still use weak passwords despite cybercriminals becoming more sophisticated. For example, according to the same Hosting Tribunal report, more than 23 million people use “123456” as their passwords.
Effective cybersecurity training should include the various aspects of good password hygiene, including:
- Not reusing the same password for two or more accounts or services
- Implementing two-factor authentication (2FA)
- Utilizing a secure password manager to store passwords
- Using randomly generated passwords
- Updating passwords regularly
It is also worth sending regular company-wide reminders for employees to update their passwords.
Identifying Phishing Attempts
Phishing attacks are the most common form of malware and are increasing in number. Experts attribute the rise of phishing attacks to post-pandemic uptake in virtual work. These attacks are also getting increasingly sophisticated and harder to spot.
For instance, business email compromise (BEC) attacks are rising. These attacks target specific individuals, usually executives and other senior officials. Hackers painstakingly collect information about the individual and create phishing emails indistinguishable from legitimate mail.
So, it is necessary to train employees on the newest phishing attacks and spot them.
Handling Unauthorized Software
As a rule of thumb, employees should not download any software without approval from the IT department. Malicious software is also getting harder to spot and can wreak havoc on the company’s network. The malware isn’t just limited to the computer or device where it was downloaded. It can spread through the network and infect other computers, as with the WanaCry malware attack.
Secure Internet Use
Employees often rely on email, social media, and the internet for their work. So, it is crucial to train them to use the internet at work safely. Furthermore, it is also a good idea to develop an internet usage policy and train your employees on its content.
Start with educating the employees on the risks of unrestricted internet usage. These risks include downloading malware and phishing websites that can capture sensitive data. Further, encourage employees to use the internet only for business purposes.
Also, train employees on proper email usage. For example, they shouldn’t register to disreputable, unsafe, suspect, or illegal websites using their corporate email. Similarly, teach the employees the basics, such as not opening attachments from unknown contacts and turning on their spam filter.
Implementing BOYD Security
Bring Your Own Device (BOYD) is becoming more commonplace. Additionally, many work-from-home employees use their personal computers and devices for work. Therefore, it is vital to cover BOYD security in your training program.
For one, inform the employees of the dangers of using public wifi. Other topics to cover in training include using VPN, protecting their devices from theft, and encrypting company data stored in personal devices.
Step 4: Make the Training Continuous
Employee cybersecurity training shouldn’t be a one-off event. Rather, it should be a continuous process that starts as soon as you onboard new employees. The security landscape is constantly shifting, so constant training helps employees stay updated on the best practices.
Consider breaking up the training into short courses throughout the year. Ideally, spreading your training to once every four months is a good start. This strategy is effective for keeping cybersecurity on top of employees’ minds.

