The Ultimate Manual To Box Shield
The corporate landscape has changed. Work is happening faster, teams are going remote, and cybercriminals are working harder.
The old-school approach to information security is no longer relevant as information flows in and out of the organization—across teams, partners, customers, and vendors—and in all directions. It’s exactly why companies are finding it challenging to protect their most sensitive assets.
Luckily, Box’s unique security offering called Box Shield can help you reduce your data and protect the information flow—all without slowing down your growth. Read on as we deep dive into Box Shield and how it works to protect your data.
What is Box Shield Anyway?
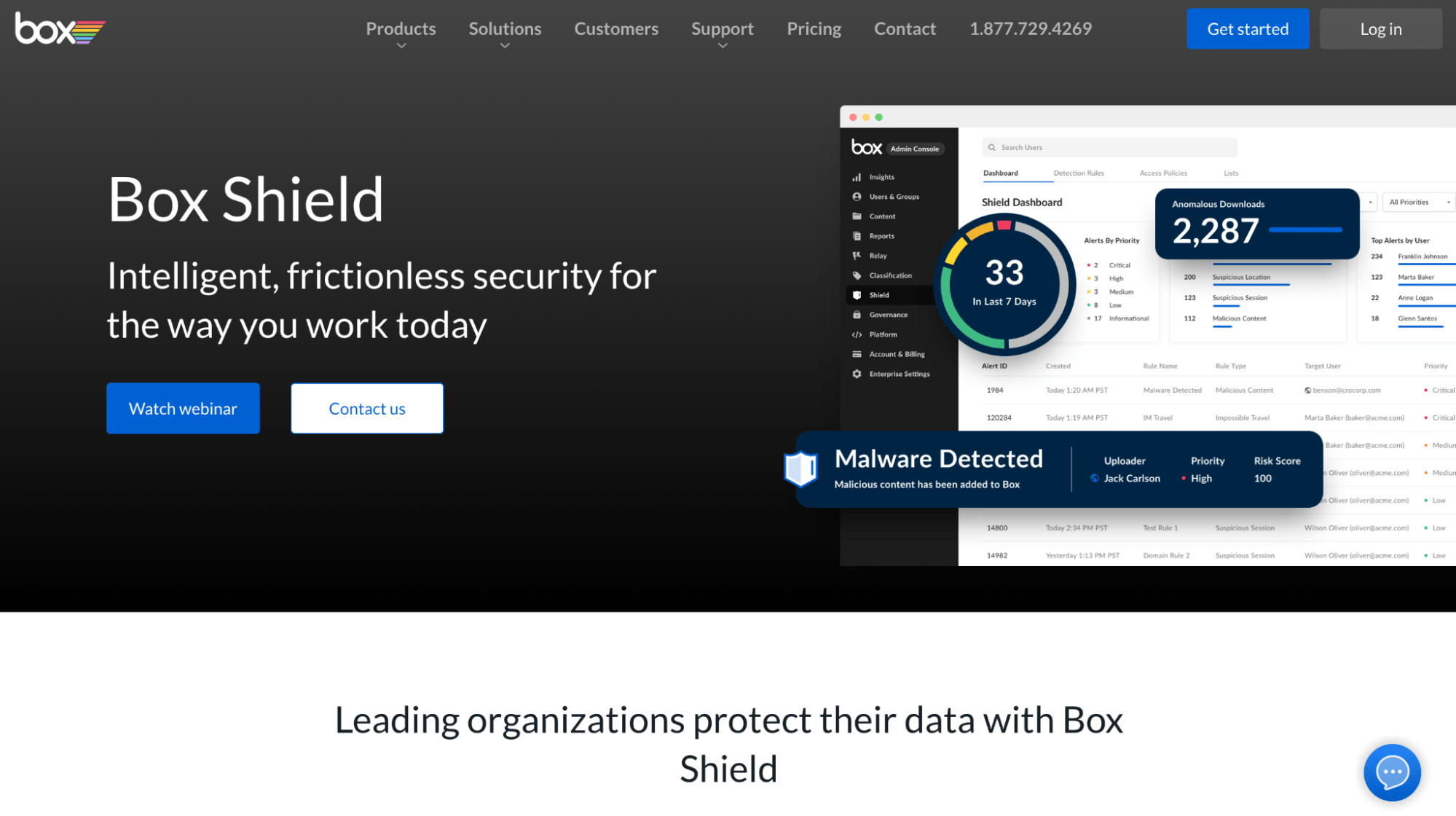
Box Shield is Box’s advanced security product designed to help businesses reduce data leak risks and safeguard information flow—both inside and outside the organization.
You can use this service to prevent accidental divulgation of sensitive data and identify potential threats as early as possible. Basically, Box Shield allows you to carry out three crucial steps to protect your data:
- Quickly detect violations of your organization’s security policies and rules and regulations.
- Enforce security controls around sensitive assets.
- Detect any compromised accounts and insider threats.
Box is already one of the most secure cloud storage and collaboration services, so it makes sense the platform is trying to offer even better protection facilities to its users. With this product, Box hopes to beef up security to reduce data breaches and ensure a smoother flow of information between stakeholders.
How Box Shield Works
Box Shield comes with a set of access controls that enable admins to classify data, enforce classification-based controls and manage classification labels. Thanks to machine learning and automation, this security product provides two crucial capabilities: Smart Access and Threat Detection.
- The Smart Access functionality allows you to define and enforce classification-based access policies to keep a check on actions, including adding external collaborators, sharing information, and downloading data.
- The Threat Detection functionality sends context-rich notifications on potential threats, such as data theft, compromising of accounts, and so on, after detecting anomalous user behavior.
Signing up for Box Shield gives you access to tons of useful features, namely:
- Define and manage security classification labels
- Native, automated classification for PII and custom terms
- Detect malware and automatically restrict downloads and sharing
- Classify files or folders manually or through automated workflows
- Detect anomalous content download behavior
- View Shield alerts and details in the Admin Console
- Enforce classification-based controls across Box native applications and third-party integrations
- Detect content access from suspicious sessions and locations
- Forward Shield alerts and classification activities to SIEM or CASB
For more context, Box Shield helps you arrange all your documents—critical and non-critical—with classification labels. So whether you store confidential healthcare information or other personal data, your team will always be aware of the importance of the file and the scale of confidentiality, thanks to these classification tags.
Let’s discuss all this in more detail.
Critical Content Classification
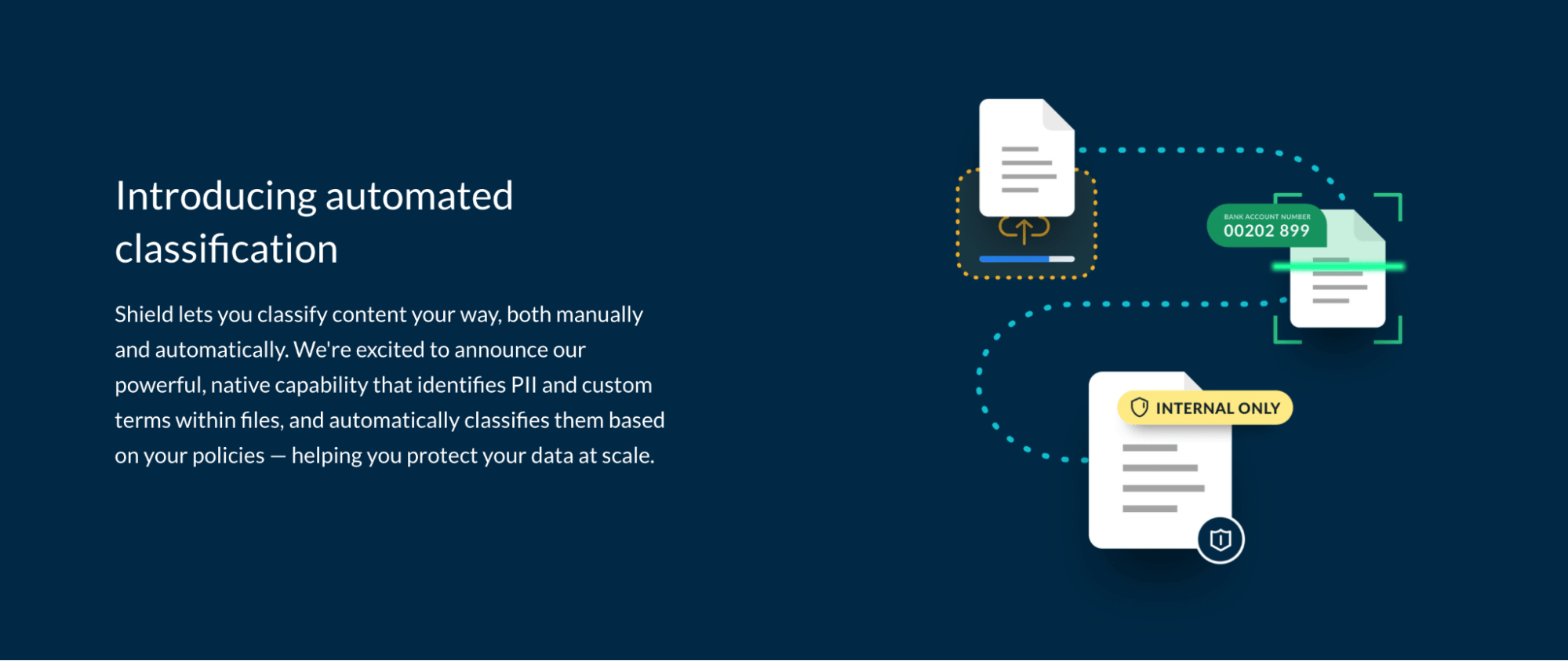
You may deal with patient healthcare data or confidential finance and HR documents—or you may have the PII of your customers. While you can collect and store any relevant data, you have to be careful when handling it. Any accidental leak can land you in a soup, where you might end up paying it forward and penalties and taxes.
Box Shield stops data leakage by helping you create labels for all your files and folders. Interestingly, you can do this either manually or automatically, whichever way you like.
Having a classification system in place educates the members about your company’s security policies. They’ll know which documents are most confidential, and hence, need to be handled with more care.
Real-Time Data Leak Prevention
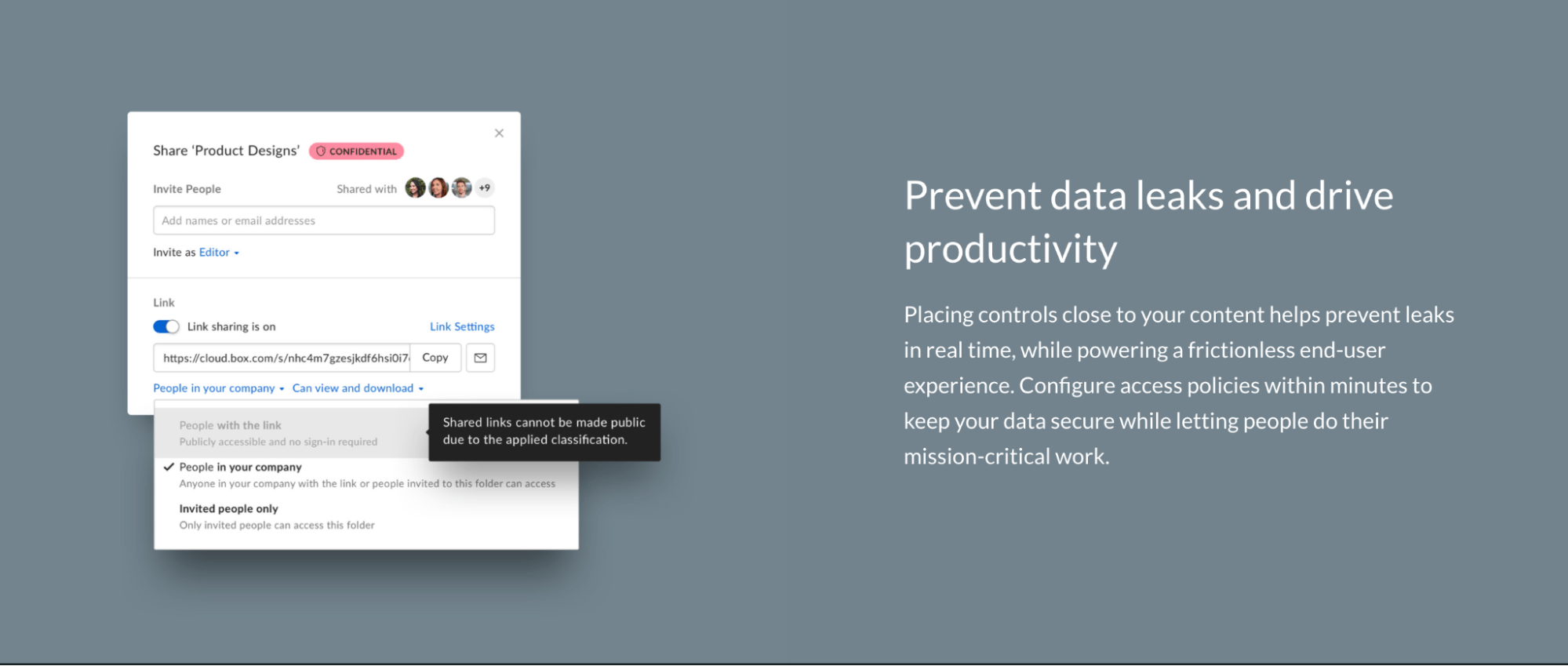
You can use Box Shield to place security controls around your content to prevent any information leaks in real-time while simultaneously creating a frictionless experience for your employees.
You can define access policies for every classification label at a granular level—each combining multiple controls, like:
- Shared Link Restriction – You can specify who can access shared links. For instance, when a file is labeled [Public], it indicates the file is safe to share with third parties. But if it would’ve had a [Internal] label, it means all sharing should be restricted to members within your organization only.
- Download Restriction – You can restrict file or folder downloads for specific applications. For example, you can stop people from downloading a file when they access the data via the Box web application, Box Drive, or the Box mobile app—or all three.
- External Collaborator Restriction – As you may have guessed, placing this restriction allows you to restrict external collaboration to only approved domain lists. You can also block domains completely based on your content‘s sensitivity. So if you label a file as [Restricted Healthcare] in Box Shield, the external collaboration will only be allowed with business partners with approved data processors.
- FTP Restriction – You can restrict FTP transfers and upload of all/selected Box files and folders.
- Application Restriction – You can decide which third-party applications and custom apps can download sensitive data from Box.
- Print Restriction – You can prevent users from printing from the Box previewer.
Existing Security Investment Enhancements
If you already have advanced security tools, Box Shield can utilize them to build a more robust cloud security portfolio. For instance, you can integrate the product’s contextual alerts that offer in-depth, actionable insights with your current CASB and SIEM solutions to monitor and analyze the overall environment.
Empowering Security Teams With Intelligent Detection
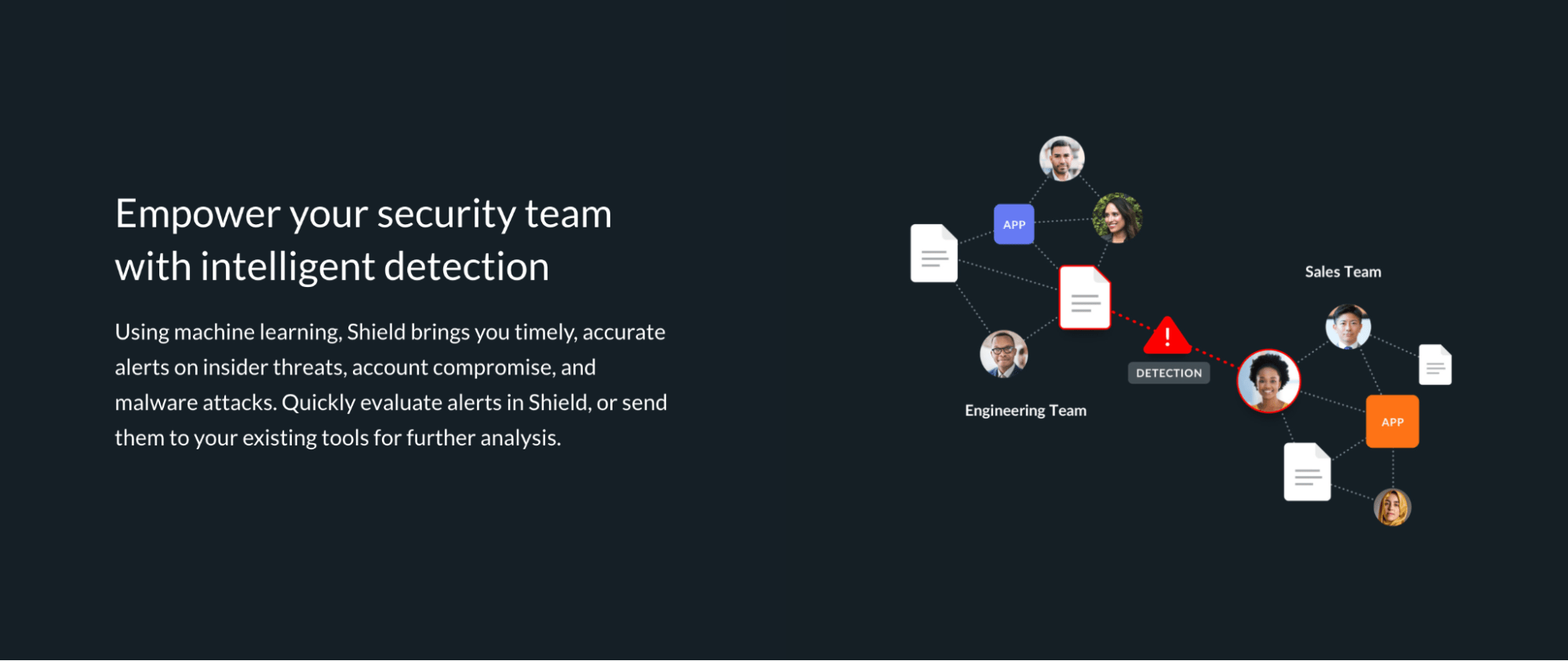
Box Shield can be incredibly helpful to detect potentially malicious and abnormal behavior from internal and external sources. Thanks to Box’s deep understanding of people collaboration on the platform and machine learning capabilities, you’re sure to receive swift, accurate alerts in the following events:
- Suspicious Sessions – You’ll be notified if Box Shield detects any potentially compromised accounts based on rapid changes in a user’s location. The product also analyzes the browsers, devices, and box applications the user typically uses to eliminate false alarms.
- Anomalous Downloads – You’ll get real-time, context-rich alerts in case of any unusual behavior that could potentially be a data theft attempt.
- Suspicious Locations – You’ll be notified if the system detects access or downloads in untrusted locations or high-risk countries. Moreover, since it’s your security team that defines location whitelists and blacklists, as well as IP ranges, this can be particularly helpful to control data breaches.
How to Protect Your Sensitive Data With Box
Box enjoys a stellar reputation, with businesses around the world trusting the platform with their most sensitive data. Thanks to its robust back-end security, you can take full advantage of its controls to decide who accesses your data and how.
In this section, we’ll discuss how you can improve your Box account security, and in turn, your organizational files.
Step 1: Sort Out Your Box Security Settings
The first step is to open the security settings panel. Then click on Admin Console, followed by Enterprise Settings.
Next, click on the Security tab located at the top of your screen.
Step 2: Choose Your Signup and Login Settings
Box’s Signup and Login section allow you to set rules for users when signing up or logging into their respective accounts. Based on your preferences, you can decide how your employees access the platform. Here’s a brief rundown of what every option does:
Self Signup
You can add users manually, but Box also permits users to add themselves to your account directly.
When you select Self Signup, you let new users sign up using your account’s custom URL. We only recommend enabling this if you aren’t too worried about your seat count.
User Email/Login
The User Email/Login option stops users from changing their Box login emails to personal addresses. You can check this box if you want to compel users to use their corporate emails when accessing the platform.
Account Creation Notification
Account Creation Notification can come in handy if you, along with other admin, want to receive email notifications whenever a new user is added. You can decide between receiving immediate notifications or a summary of new users once a day.
Failed Logins
Turning on this option will keep you in the loop regarding failed logins, helping you identify unauthorized access. Moreover, you can customize the number of login attempts before you receive a notification.
Step 3: Activate 2-Step Login Verification
You can make it mandatory for employees to provide a second verification source before accessing company assets—something we highly recommend enabling.
Managed Users
You can enable 2-factor verification for everyone who has access to your organization. Just check to Require all managed users to have additional verification for unrecognized logins, and everyone will have to set up 2-step login verification.
External Users
Yes, Box makes it possible to enable 2-factor verification for external collaborators as well. To do this, select Edit Configuration and then activate 2-factor verification from the range of options.
And that’s not all! There are several other sections concerning password requirements, FTP restrictions, and session durations that you can fine-tune. Each of these options is specifically designed to boost your Box account security and prevent potential data breaches and leaks.

