Best Full Disk Encryption Software Products of 2022
In today’s digital world, unprotected or inadequately protected data is the biggest cybersecurity risk for organizations of all sizes. When data is unencrypted, anyone can access the information, but when you encrypt data, no one can read the data without the right encryption key. Full disk encryption provides an omnipresent layer of protection across an entire storage device, be it a solid-state drive (SSD) or spinning hard disk.
Read on as we present our list of the five best full disk encryption software products to protect your data from prying eyes.
IBM Guardium Data Encryption
IBM requires no introduction in the technology world, having created a name for itself over the past century. The company acquired Guardium back in 2009 to provide unparalleled encryption capabilities to protect on-premises structured and unstructured data.
Essentially, IBM Guardium Data Encryption is an enterprise-level data security solution that business leaders can rely on to protect, monitor, and increase their systems and data to prevent data breaches. You can perform encryption and decryption operations without making any changes to databases, applications, or networks. Even the performance impact is minimal as the software works quietly in the background.
The full disk encryption software also monitors your data activity to provide you access to critical security insights. You can expect to have detailed information about your sensitive data, applicable threats, and potential solutions to eliminate those threats.
Centralized key and policy management, granular encryption of files and folders, and compliance adherence are a few of the other features offered by IBM Guardium Data Encryption.
Pros
- Suitable for large companies
- Advanced analytics and reporting capabilities
- Tailor-made encryption solutions
- Saves money in the long run
Cons
- No free trial
- Error logs are hard to understand
- Steep learning curve
Pricing
IBM Guardium Data Encryption doesn’t have pricing information published on its website. You have to contact a Guardium expert to get a customized quote.
Apple FileVault
As the name suggests, Apple FileVault is an excellent full disk encryption software product for Mac users. It’s built into specific versions of the macOS X and is AES 128-bit and AES 256-bit compatible.
Apple FileVault requires you to create a strong, unique password for your data before encrypting and encoding your entire startup disk. The full disk encryption software protects your entire system’s integrity and is suited to an office or home environment, where your computer won’t go into someone else’s hands.
What’s more, this software product is validated as Federal Information Processing Standard (FIPS) 140-2 certified on the latest versions of macOS. This indicates successful independent testing of the product and confirms it adheres to specific cryptographic implementation requirements. In other words, no major known cryptographic weaknesses were found when the full disk software product was tested.
Pros
- Free for Mac users
- Increase your entire system
- Easy recovery via iCloud account
- Locks your screen
- Checked for cryptographic weaknesses
Cons
- Access and data security are highly dependent on your password
- Can slow things down when working on large projects or files
Pricing
Apple FileVault is free for Mac users.
Microsoft BitLocker
Microsoft BitLocker is a full disk encryption software product for—you guessed it—Windows 10 devices. You can use it to encrypt a particular disk partition or the entire hard disk. It uses the AES 128-bit or AES 256-bit key algorithms for encryption, and while BitLocker isn’t IPS 140-2-certified, the cryptographic modules it uses are, so it’s ultimately on par with Apple FileVault.
Microsoft BitLocker approaches things on a wider scale instead of focusing on individual file encryption. The software works because it fully monitors the operating system and can detect when firmware-level malware is trying to infect it. It can easily detect a rootkit messing with your system and has features to prevent or control a cold boot attack, too.
That said, authentication options are limited when using Microsoft BitLocker. The software product is intended to be used with a Trusted Platform Module (TPM), and authentication is completed after specifying a PIN or storing a key on a flash drive, which the user has to insert to boot the system.
It also doesn’t have a Windows 10 home encryption solution, so if you want to encrypt files yourself, you’ll have to look for other options on our list.
Pros
- User-friendly
- Free for compatible operating systems
- Multiple logins and decryption methods
- Encrypts your entire drive
Cons
- Limited authentication options
- Slow performance at times
Pricing
Microsoft BitLocker is free for compatible operating systems, namely Pro, Enterprise, and Education versions of Windows, and Microsoft Server. It can also be bundled with Microsoft’s cloud.
McAfee Complete Data Protection
McAfee Complete Data Protection is a comprehensive data security solution for your organization, comprising data loss prevention, full disk encryption, device control, and cloud storage protection. It offers full disk encryption capabilities, among other features, for enterprises that are running Windows and macOS X systems.
The software allows you to fully encrypt hard drives on desktops, laptops, and servers. In addition, it also delivers storage encryption capabilities for individual files and removable media. You can expect fine-grain controls for all your data and devices with this software product.
McAfee Complete Data Protection offers users the choice to improve upon OS-based full disk encryption. The tool can add central management features to these end-user-based hard disk encryption applications. What’s more, you can use it to monitor real-time events, which can later be compiled using McAfee’s advanced reporting and auditing capabilities.
McAfee Complete Data Protection is available in two versions: McAfee Complete Data Protection and McAfee Complete Data Protection Advanced. It’s the advanced version that comes with data loss prevention (DLP) capabilities. Aside from this feature, both versions can be centrally managed through McAfee ePolicy Orchestrator software, support AES 256-bit encryption, and are FIPS 140-2-certified.
The software product also natively supports multi-factor authentication, along with Active Directory integration, public-key infrastructure, and other enterprise authentication-related services.
Pros
- Simple and user-friendly interface
- Effective data protection solution that prevents data leakage
- Efficient technical support
- All in one tool for organization and personal use
Cons
- Confusing pricing
- Doesn’t offer explanations for blocking certain sites or downloads
- Can be slow at times
Pricing
Although it’s better to contact the sales department for a detailed price breakdown, it’s reported the cost per license starts from $67.99 for bulk licensing (501-1000).
DiskCryptor
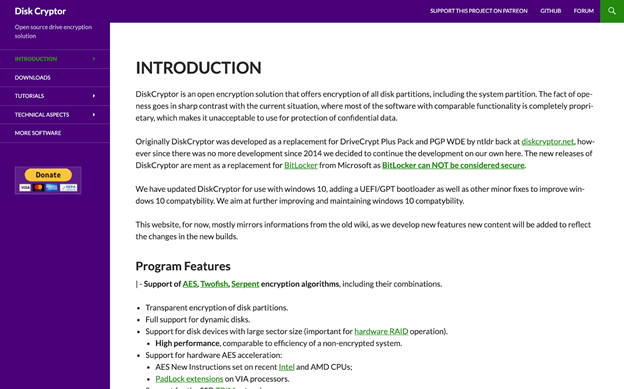
Designed for Windows, DiskCryptor is an open-source, full-disk encryption software product that allows you to encrypt the whole system/boot volume and other internal or external hard drives.
It’s incredibly user-friendly and has some unique and impressive features. For instance, you can add one or more keyfiles to the software to boost security, which is an additional feature besides password-protected partitions. The keyfiles can be in the form of files or folders, and if set up accordingly, would be needed before mounting a group or decrypting or volume.
DiskCryptor supports encrypting several volumes at once, is compatible with a RAID setup, and can pause encryption to let you reboot or remove a hard drive during the process. ISO image encryption to produce encrypted CDs/DVDs is another possibility.
You can view or modify data on a volume that’s encrypted using DiskCryptor while the drive is mounted. No need to decrypt the entire drive to gain access to files. What’s more, the volume can be dismounted in seconds, rendering the drive and all data on it unusable until the password or the files are entered.
Another feature we really like about DiskCryptor is if your computer reboots while a drive is mounted and readable, it’ll auto-dismount and become unusable until the credentials are re-entered. This really boosts the overall security of your data and files.
Pros
- Free, user-friendly software
- Supports key files and RAID arrays
- Auto-dismounts to make data unusable during glitches
Cons
- Tends to glitch
- Software is somewhat antiquated
- Additional tools aren’t always useful
Pricing
As mentioned, DiskCryptor is a free full disk encryption software product.
How to Pick Your Full Disk Software Products
In this section, we’ll review how you can find the best full disk encryption software for your requirements. Let’s take a quick look.
Step 1: Decide Whether the Full Disk Encryption Software Product is for Individual or Business Use
If you plan to use the software for individual use, you can look for a single home use license as it’s much cheaper and usually involves a one-off payment.
But if you want the software for business use—or plan to protect several members of the family or multiple computers—you may need a bespoke plan that can efficiently support multiple or unlimited users.
Step 2: Consider Your Operating System
Depending on whether you have a Mac or Windows, you’ll want software that’s compatible with your operating software. You may find software packages that are dedicated to either Mac or Windows, but some solutions work with both systems.
Step 3: Decide Between Local or Cloud
Infected files have a larger size than their originals because of the encryption process. Many programs end up compressing in separate files to reduce their sizes, but over time, you’ll find them taking up a lot of your storage space.
If you plan to encrypt your company’s financial information, personal files and photos, account login credentials, and so on, you’re unlikely to need a lot of storage space. This is because you can store the encrypted files on your device or any secondary device.
But if you plan to encrypt everything virtually, the data will keep growing. In these cases, opting for remote/cloud solutions would be much preferable. This is even more relevant in the case of businesses that require a lot of storage space.
Look for software that lets you link up your existing storage accounts like Dropbox and Google Drive or offer a paid cloud storage solution.
Step 3: Determine the Suitability of the Encryption Method
While your top priority is to find a full disk encryption software product that’s rated well, you also want to ensure the encryption method used isn’t outdated. In most cases, AES 256-bit is the standard, but you’ll also find other methods, such as Blowfish, GOST, and Camellia.
To help you determine the right method fit and understand your encryption scope, here are a few questions you should consider:
- Do you want to encrypt entire drives or just your operating system?
- Do you want to encrypt external storage devices? Or would you prefer sending encryption files there?
- Do you want software that can send encrypted files to cloud hosting services? Or are you okay sending them via mail?
Remember, any well-known encryption method in modern software is going to be 99.999% secure, but it’s always better to understand the encryption method and the scope.
Step 4: Understand the Full Disk Software’s Usability
While we’ve done our best to include user-friendly software products on our list, you may still face difficulty with a few options. That’s why you want to find out the learning curve involved before putting down your money.
Try to look for software that allows you to encrypt files from the right-click context menu or simply by dragging and dropping files into a ‘locker.‘ In case you plan on encrypting a lot of files, you’ll also want a tool that offers easy navigability.
In addition to the above, you’ll obviously want full disk software products that fit within your budget. We also recommend checking out the extra features offered by each solution. Give bonus points to solutions that include a file shredder to permanently delete files or a password manager to store your password securely.

