The 5 Best Endpoint Security Tools and How to Decide
2020 has seen a surge of businesses, schools, and municipalities transitioning to remote work as the norm. As these organizations spread endpoints far and wide, connecting to a wider range of unprotected networks, they open themselves up to cyberattacks.
According to Accenture, there’s been a 67% increase in security breaches over the past five years. Discovering and containing these breaches quickly is only possible with the best endpoint security software.
Below are reviews of the 5 of the top products on the market today. These vendors consistently rank highly and offer a range of services you can mold to fit your needs. I’ll finish with a step by step process to help you pick the best endpoint security software for your organization’s particular IT environment.
Kaspersky Business
Pricing:
- Kaspersky Endpoint Security for Business Select: Starting at $335/year for 10 desktops and servers
- Kaspersky Endpoint Security Cloud: Starting at $300/year for 10 desktops and servers
Kaspersky Business is one of the most active forces for cyber safety in the world. They respond to the most dangerous advanced persistent threats, analyze the methods and tools of the attackers, and constantly evolve the tools they offer.
Kaspersky Business delivers multi-layered, automated endpoint threat defense and systems hardening that will keep your data secure across multiple environments: PC, Mac, Linux, iOS & Android.
Deploy in the cloud, on premises, or both, and build out a system that fits your needs with one of their three progressive feature packs:
Endpoint Security for Business Select
- Security for PC, Linux & Mac
- Mobile Threat Defense
- Security policy adviser
- EDR agent
- Application Control for PCs
- Device and Web Controls
- Ransomware protection
- Cloud-assisted intelligence
- Single management console
Endpoint Security for Business Advanced
- Role-based access control
- Adaptive Anomaly Control
- Encryption management
- Vulnerability and Patch management
- OS & 3rd party software installation
- Application Control for servers
- Integration with SIEM systems
Endpoint Security for Business Total
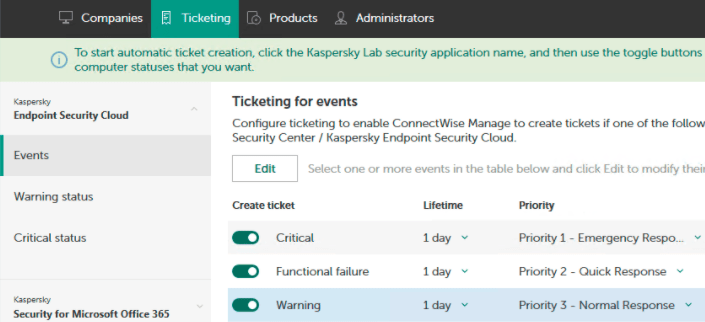
All of the core Kaspersky technology is developed in-house, which means that all of your protection services are integrated, efficient, and secure. Regardless of the feature pack, your license includes a unified set of EDR tools you can control from a single console.
Migrating to Kaspersky from a third party is straight-forward, and they offer consulting, configuration, and post-migration audit services to organizations with a complex infrastructure and security needs.
ESET Endpoint Protection
Pricing:
- Starting at $190 for 5 devices
ESET is a longstanding player in the cybersecurity market with endpoint protection solutions aimed at small, mid-sized, and enterprise companies. You can manage their platform via the cloud or on premise, both options are included in the license.
Deployment is easy, navigation is intuitive, and updates are seamless. ESET Endpoint Protection works across multiple platforms and protects all your computers, tablets, smart phones, file servers, and virtual environments.
Some of the best features include:
- Network Attack Protection stops ransomware attacks at the network level with advanced malware detection and disrupts malicious payload delivery.
- ESET Threat Intelligence helps businesses to respond to novel threats by providing information about the latest threats from more than 100 million sensors analyzed by ESET’s R&D centers.
- Advanced Memory Scanner protects against fileless malware that exists almost entirely in RAM (zero footprint attacks) by recognizing malicious processes in trusted programs, like PowerShell.
ESET Endpoint Protection for small business works for up to 250 seats. For more than that, you will need one of their solutions for mid-sized businesses (251-999 seats) or enterprise (1000+ seats). These plans bundle multiple products together for complete endpoint protection, so the small business ESET Endpoint Protection license includes:
- ESET Endpoint Security
- ESET Endpoint Antivirus
- ESET File Security
- ESET Mail Security
- ESET Mobile Device Management
- ESET Virtual Security
The flexibility of the licencing with ESET is welcome. You can add additional devices, mix and match licenses, and transfer licenses from one computer to another.
With a range of deployment options, and comprehensive endpoint protection included at all price tiers, ESET is a sensible choice for many companies.
CrowdStrike Falcon Endpoint Protection Enterprise
Pricing:
- Starting at $15.99 per endpoint/month
Crowdstrike is one of the most popular cybersecurity solutions on the market today because their tools are lightweight and powerful. Customers can choose the specific set of Crowdstrike services they need, and rest assured the new system won’t bog down network connectivity or overwhelm administrators.
In terms of complete endpoint security software, we recommend Crowdstrike Falcon Endpoint Protection Enterprise. There is a lower tier (Falcon Pro), but it doesn’t come with endpoint detection and response, which is essential for breach protection, especially from targeted attacks.
With Falcon Enterprise, you get a unified suite of tools that provide multiple layers of security, including:
- Falcon Prevent: Next-Generation Antivirus
- Falcon X: Threat Intelligence
- Falcon Device Control: USB device control
- Falcon Firewall Management: Host firewall control
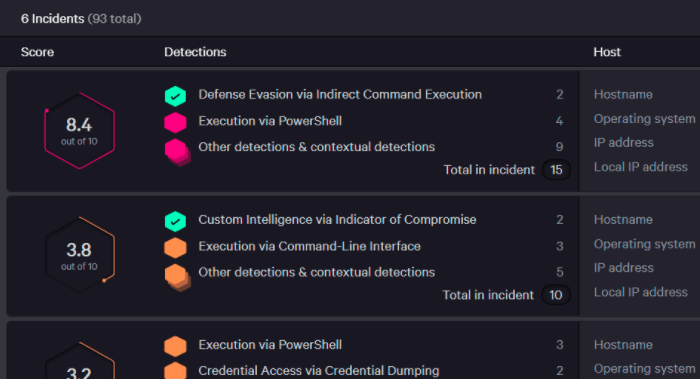
- Falcon Insight: Endpoint detection and response
- Falcon Overwatch: Threat hunting
The suite costs $192 per year/endpoint for less than 250 endpoints, with price breaks available for volume licensing. Falcon for Mobile must be purchased as an add-on to the Falcon Enterprise bundle.
The platform is entirely cloud-based, which means there are no server fees and it’s easy to scale. Agents are lightweight and constantly in touch with Crowdstrike’s central hub, staying up to date about the latest threats worldwide.
The management console prioritizes threats and helps IT teams hunt for threats and respond to attacks. After an event, they can see an entire process tree that shows how attackers tried to breach the system. Administrators can remove infected endpoints from the network, make sure they have eliminated the threat completely, and bring the restored device back online.
For traditional IT managers, the idea of cloud-based EDR may seem a little risky, but the age of persistent threats, the value of CrowdStrike’s speed and agility is becoming more and more appealing.
Trend Micro Smart Protection for Endpoint
Pricing:
- Contact sales
Trend Micro is another a la carte cybersecurity vendor with a range of high-powered products customers can mix and match to get the coverage they need.
In terms of their overall best endpoint security software, Trend Micro Smart Protection for Endpoints Suite is a bundled offer that provides everything a company needs to keep their information secure.
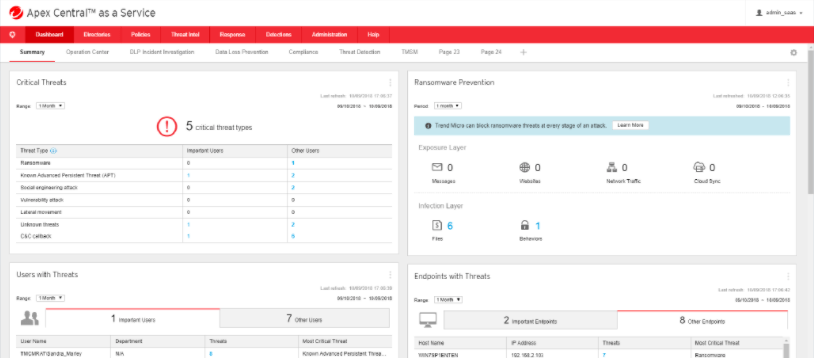
The key endpoint-focused component of the suite is Trend Micro ApexOne, which provides protection capabilities like intrusion prevention and application control for gateways and endpoints.
You can purchase Apex One as a stand alone product, but you would need to integrate it with tools from other vendors to secure every layer protection afforded by the Smart Protection Suite.
Deploy on premise, in the cloud, or a mix of both. Regardless of deployment, you can control every facet of the endpoint protection suite from a central console. With advanced detection, you can quickly understand and visualize how threats are spreading across multiple systems, eliminating false positives with noise cancellation techniques.
Surface real attacks and respond rapidly with an integrated suite of programs leave no gaps in your security.
The bundle includes the following Trend Micro services:
- XGen™ Anti-Malware
- Vulnerability Protection
- Virtual Desktop Integration
- Mac and Windows Security
- Server Security
- Endpoint Application Control
- Endpoint Encryption
- Mobile Security and Management
- Advanced Detection and Response
You can upgrade to Smart Protection Complete to get additional protections for web activity, email, and collaboration, including:
- Messaging Gateway
- Mail Server Security for Microsoft Exchange
- Mail Server Security for IBM Domino
- Instant Messaging Security for Microsoft Lync
- Microsoft SharePoint Security
- Security for Microsoft Office 365, Box, Dropbox, and Google G Suite
- Secure Web Gateway
All plans come with 24/7 support and integrated DLP. Adding new modules to your suite of services is easy, making Trend Micro one of the most flexible options on the market.
Bitdefender
Pricing:
- Starting at $55.49 per year for 3 devices
Bitdefender has been winning people over with GravityZone, frequently listed as an overall best endpoint security software for many business types. They offer expansive protection capabilities for any type of endpoint, including IoT devices, to keep your entire network safe from all kinds of attacks.
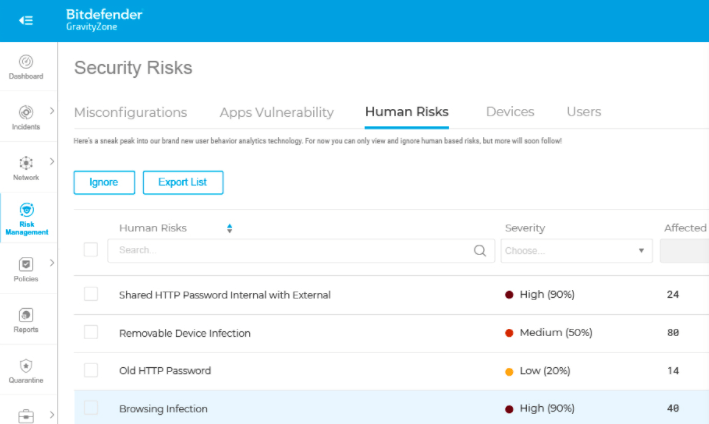
GravityZone is a single agent, single console solution that gives you a complete picture of all the threats and potential problems across all endpoints. Risk management and analysis is streamlined, as misconfigurations, vulnerabilities, and human risks are prioritized on an intuitive dashboard.
For small to medium-sized businesses, Bitdefender has three plan options with more advanced features included with the higher tiers:
GravityZone Business Security
- Endpoint risk analytics
- Web threat protection
- Device control
- Application blacklisting
- Two-way firewall
- Local and cloud machine learning
- Advanced anti-exploit
- Process inspector
- Automatic disinfection and removal
- Network attack defense
GravityZone Advanced Business Security
- Supports mobile devices
- Supports Microsoft Exchange
- Smart centralized scanning
- Fileless attack defense
- Role-based access control
GravityZone Elite
- Application control
- Sandbox analyzer
- Tunable machine learning
- Ransomware mitigation
For larger organizations with advanced security challenges and regulatory requirements, Bitdefender offers 2 enterprise versions Gravity Zone: Ultra Plus and Elite. These come with incident visualization, root cause analysis, anomaly defense, and other features necessary to monitor and secure networks that span thousands of devices.
For smaller companies, or those that are looking to transition to next generation endpoint defense, GravityZone Business Security is one of the strongest options on the market.
You’ll need to upgrade to Advanced for mobile endpoint coverage and protection from zero footprint attacks, but other than that, it is one of the most complete entry-level plans available.
How to choose the best endpoint security software
Step 1: Map network topography
One of the biggest limiting factors between different vendors are the range of endpoints they cover and operating systems they support. Before you start making calls, be sure to completely map out your entire network: all physical, virtual, mobile, and cloud-based endpoints, including email.
Since your network is likely to grow, and it’s less of a headache to switch vendors, you want to factor in the scalability. How many devices do you need to support now, and are you likely to be supporting in the future?
Consider deployment, as well, especially if regulatory requirements limit you to an offering with on premise or hybrid options. CrowdStrike’s native cloud endpoint protection products are phenomenal, but there’s no on premise deployment available.
Step 2: Define necessary endpoint capabilities
Antivirus tools are mission critical for any organization, and all of the best endpoint security software has the ability to block dangerous programs and web-based threats. In today’s cybersecurity landscape, however, antivirus is only part of the picture when it comes to hardening endpoints to withstand sophisticated attacks.
As you think about the capabilities you need, work backwards from your IT team’s dream situation. In other words, what do you need for your administrators to minimize:
- MTTI: Mean Time To Identify a threat
- MTTC: Mean Time To Contain a threat
These are the deliverables of your potential endpoint security software, so keep those in focus as you consider what works best in your particular situation.
Here, it’s going to be helpful to get input from the IT staff that will be interfacing with the system directly. What are the most pressing threats? What are the current gaps in security? What level of control do they need over their EDR to visualize and respond to threats?
Step 3: Budget long-term for complete endpoint protection
Information sharing among the cybersecurity sector is on par with airlines—after a hack, the community at large dissects the incident and comes up with strategies and improvements to prevent it from happening again.
Since serious endpoint protection products must protect against known threats, and even zero-day attacks are quickly made public, it’s no surprise that all of the top products offer a similar range of services.
For you, the question becomes matching the functionality you need with a plan or a la carte selection of services from a vendor that supports your entire IT infrastructure. Make sure you are covering all your bases.
For example, ESET Endpoint Protection includes mobile devices at a fairly low cost, whereas it only comes with GravityZone Advanced Business Security, or as an add-on with CrowdStrike products.
Get in touch with sales at this point. Confirm that the product will support the network topography you outlined in step one, and price out total coverage for the services you identified in step two, taking into account future growth.
Budget increased resources for IT in addition to the costs of the endpoint security software. As IT responds to novel threats and oversees a growing number of endpoints, you want to be sure that they are appropriately staffed, and trained in how to configure and monitor the new system.
After all, you need lean performance in your specific environment. Bitdefender has excellent scanning capabilities, for example, but it can cause the network to drag during run time if your IT team hasn’t set a comprehensive list of exclusions.
Step 4: Deploy the new system and test it
One of the key reasons these 5 vendors made our list of the best endpoint security software is the ease of deployment. Whether this is a new system for the company, or you’re migrating from a third party, you can start implementation on Friday afternoon and have thousands of devices better protected by Monday morning.
An effective system relies on the humans that use it, and you need to invest in security awareness training. Even the absolute best endpoint protection can be compromised instantly by a weak password or plain old human error.
Everyone at your organization needs to understand their role as the frontline defense against cyberattacks.
In addition to training, you can work with a company like KnowBe4 to truly test your new system and the people using it. KnowBe4 simulates phishing attacks, which can provide a valuable lesson in a safe environment.
A “whoops” that could have cost millions is turned into a teaching moment.

