Best Encryption Software of 2022
With rising cybersecurity incidents, implementing stringent data security measures is more important than ever. Encryption is an excellent way to secure your data. This method involves locking and unlocking data so that unauthorized users can’t access your information even if your files inadvertently fall into the wrong hands.
To this end, encryption software is part and parcel of proactive cybersecurity. However, there are a plethora of options available on the market. So, how do you choose the best software for your needs? This review features a detailed list of the six best encryption software currently on the market.
Folder Lock – Best Encryption Software for Multiple Devices
Folder Lock is a versatile encryption tool that offers two main options for protecting your information. First, Folder Lock hides your files with kernel-level filtering, so they cannot be detected in Windows. Simply drag and drop the file you want to lock into Folder Lock, and it disappears from your device. Then, access Folder Lock using your password to view locked files.
You can even lock an entire drive or program. Alternatively, you can encrypt your folder contents with 256-bit encryption. This encryption is virtually impenetrable and offers the maximum protection you could hope for.
You also get additional nifty features like a File Shredder. For example, the file shredder deletes and re-writes files, so they are irrecoverable. It’s a valuable feature when deleting the original unencrypted files. You also get the Wallets feature for storing your credit or debit card information in an encrypted folder.
The best part about Folder Lock is it works across devices. So, if you regularly access personal or work files from multiple devices, this is the encryption software for you. You can use Folder Lock with Windows, Android, and Apple devices, which covers all your hardware.
Folder Lock is also affordable. You can get the app for a one-time fee of $39.95.
However, Folder Lock is far from perfect. This encryption solution is most suitable for personal use on handheld devices. It is not robust enough for business use, especially if you are worried about compliance issues. In addition, it lacks more sophisticated features like Public Key Cryptography.
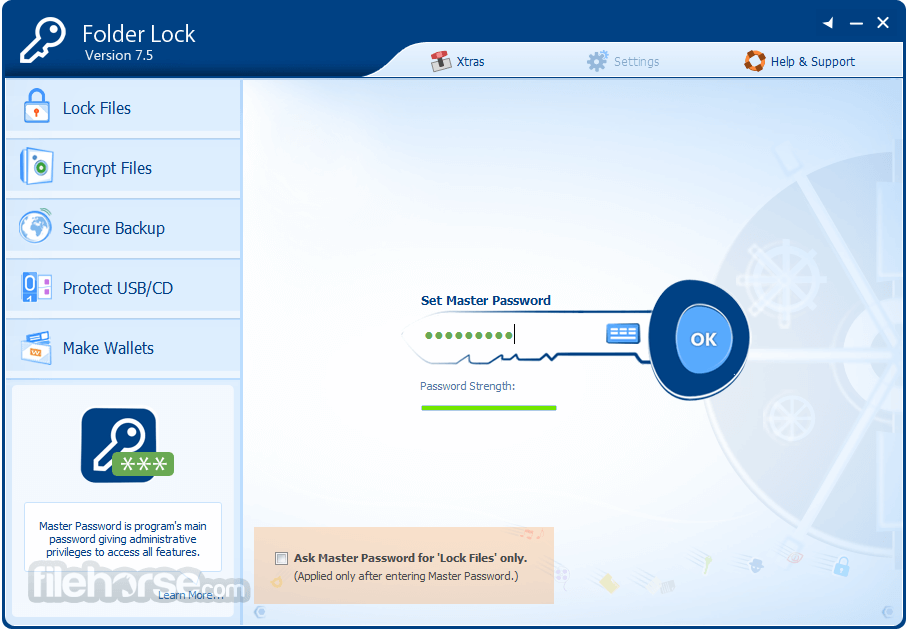
Additionally, the app only offers cloud encryption backup at an additional fee. This service isn’t included in the original price. Finally, Folder Lock comes with a backdoor. Your serial number also doubles up as a password. There is an option to deactivate this feature in the settings. But, it would be far safer if the backdoor didn’t exist in the first place.
Still, Folder Lock is a solid choice if you need to secure data across your hand-held devices. You also get bonus features like Protect USB that lets you transport your encrypted files on external devices without requiring the app on the device. It is also easy to use and has an intuitive interface.
NordLocker – Best Encryption Software for Cloud Storage
NordLocker from Nord is an ideal encryption option if you already store all your essential data in the cloud. Cloud storage comes with inherent risk, so this encryption software can help you rest easy knowing your data is secure.
With NordLocker, you essentially get rid of the middle man, so you don’t have to encrypt files and upload them to the cloud. Instead, you now have the same provider handling the entire process. The data is stored securely on NordLocker Cloud. Alternatively, you can keep the encrypted files locally on your device.
The encryption tool uses AES-265 encryption, which is currently the industry’s strongest encryption. It is also straightforward to use. You don’t need to be an IT expert to protect your information. Simply drag and drop your files to NordLocker, and the software encrypts them for you. You’ll also be prompted to permanently delete the original unencrypted files, which is a nice touch.
NordLocker supports Windows and Mac OS. As a bonus, you can install the software on unlimited devices at no extra cost. This model is convenient if you stick with your preferred third-party cloud storage service. In this case, changes to your encrypted files automatically sync across all your devices. Then, simply install the software on every computer you use to access the files.
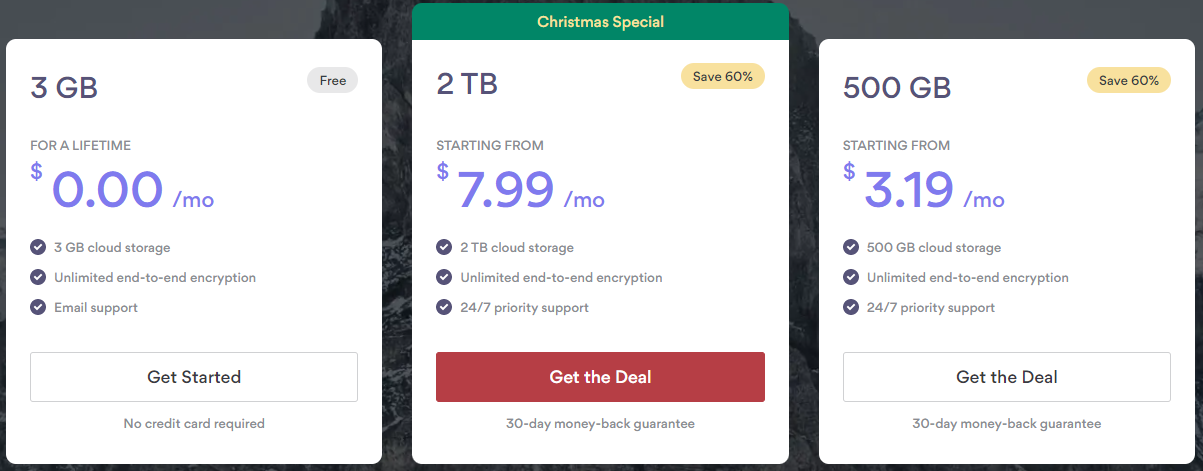
The software’s pricing also offers terrific value for money. There’s a free plan with 3GB of cloud storage. The free plan may be sufficient for personal use. But, you’ll need to upgrade to enjoy more cloud storage. The paid plains include:
- 500 GB Cloud Storage for $3.19 per month.
- 2 TB Cloud Storage for $7.99 per month.
While NordLocker covers all the bases for most users, it is not a perfect encryption solution. For example, the software doesn’t have two-factor authentication. So, you’ll need to be keen to choose a strong master password. This is especially true since the software doesn’t rate your password strength.
Nevertheless, it’s hard to beat NordLocker if you are looking for cloud-based encryption software. It is handy for individuals, small teams, and small businesses. The pricing is also attractive for this market.
AxCrypt Premium – Best Encryption Software for Secure File Sharing
 AxCrypt Premium is reliable encryption software that keeps your file safe from prying eyes. But, the software truly shines with its secure file-sharing capabilities. It has a quick share button that allows you to securely send files to anyone with an AxCrypt account, including the free tier. In addition, you only need the recipient’s email address associated with their AxCrypt account.
AxCrypt Premium is reliable encryption software that keeps your file safe from prying eyes. But, the software truly shines with its secure file-sharing capabilities. It has a quick share button that allows you to securely send files to anyone with an AxCrypt account, including the free tier. In addition, you only need the recipient’s email address associated with their AxCrypt account.
The software is also straightforward to use. It has a simple interface with additional nifty features to make your work easier. For example, the software embeds to your Windows context menu. So, you can encrypt or permanently delete files by right-clicking on them.
Speaking of deleting files, AxCrypt works like a file shredder. Even with forensic software, any file you delete using the program cannot be recovered. The program overwrites the data automatically, so you don’t need a third-party deletion tool to get rid of your original unencrypted files.
Alternatively, you can encrypt files by simply dragging and dropping them to AxCrypt. Furthermore, working on your encrypted files is super easy. You don’t need to decrypt, edit, and encrypt the file again. Instead, you can go straight to editing as soon as you open the file. Then, the software automatically encrypts your file again when you hit save.
The Premium account comes with fantastic security features. For example, you get cloud storage awareness, key sharing, subfolder encryption, and storage management with this tier.
The software is also priced favorably. There’s a free version, but you’ll want to upgrade to the paid plans for more robust security. These plans include:
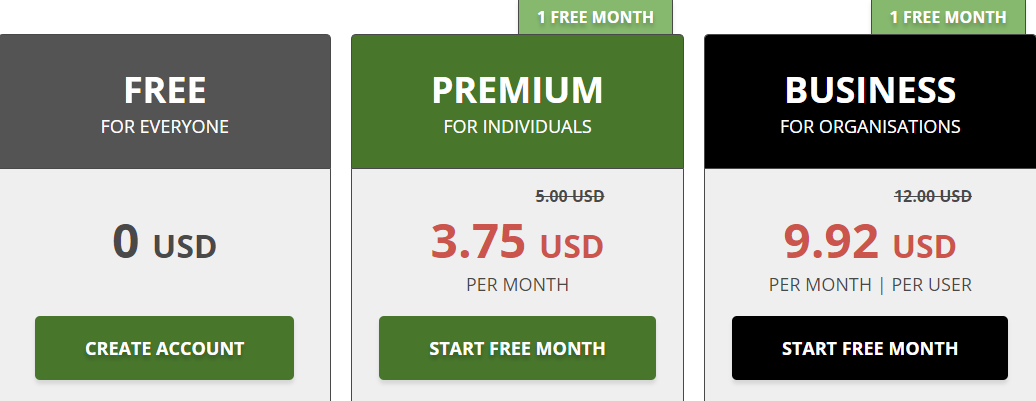
The Premium plan is sufficient for most individuals and small businesses. Or, you can opt for the Business plan that comes with add-ons such as Master Key, Business Priority Support, and Business Admin. You can also try out any of the plans for free for one month.
On the downside, AxCrypt doesn’t come with the bell and whistles that we’ve seen in some of these solutions. For instance, the software simply sticks with AES encryption which is frankly as good as you get. But, some users may want to choose from 10+ encryption algorithms. Either way, this software is a strong choice, especially if you wish to send files securely.
CryptoForge – Best Software for Encrypting Text
CryptoForge is unique in that it doesn’t come with a user interface. Instead, you use the Windows context menu to encrypt and decrypt files. Then, simply right-click on the file you want to encrypt and choose CryptoForge from the context menu. This design makes the software easy to use and light on your processing power.
The software does everything you need a good encryption tool to do. But, CryptoForge also allows text-only encryption. Here, you can type your confidential message in the text module. You’ll find the text editor in the notification area’s main menu. You can also include attachments. Then encrypt the message and files and send them securely via email.
CryptoForge is very easy to use. But it also comes with some advanced options for people who know their way around encryption. For example, you can choose your encryption algorithm. The possibilities here include AES, GOST, Triple DES, and Blowfish. You can even overwrite files up to 99 times before deleting them.
The software also comes with a handy file shredder to ensure your deleted files are irrecoverable. The software even lets you encrypt files as you copy them. This way, your duplicate file is encrypted when it’s done copying.
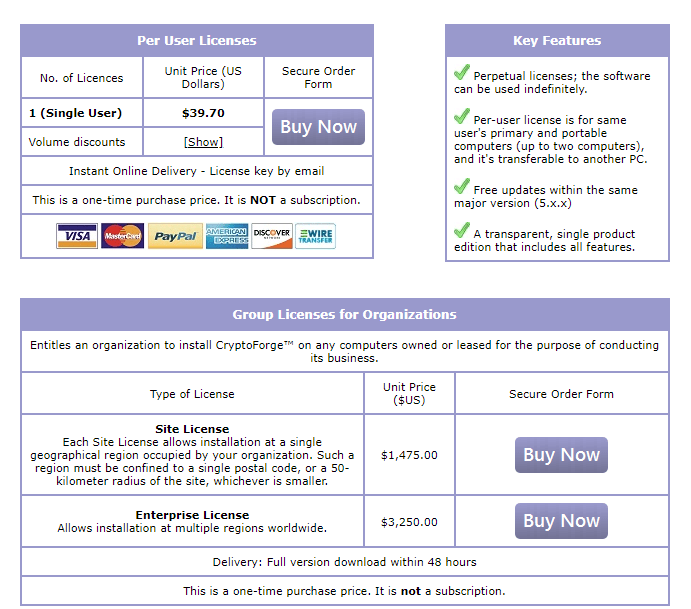
CryptoForge charges per-user licenses. You pay a one-time fee of $39.70 to enjoy the service indefinitely. There are also pricing options for enterprise users. This way, you can install the software on unlimited devices within one geographical location.
However, the software does have its downsides. For instance, the software doesn’t offer a free option. So, you are out of luck if you are looking for a simple, free encryption tool for personal use. Otherwise, CryptoForge is an excellent encryption tool that delivers on its promise. It’s beneficial if you’d like to send confidential text messages via email or messaging apps.
VeraCrypt – Best Free Encryption Software
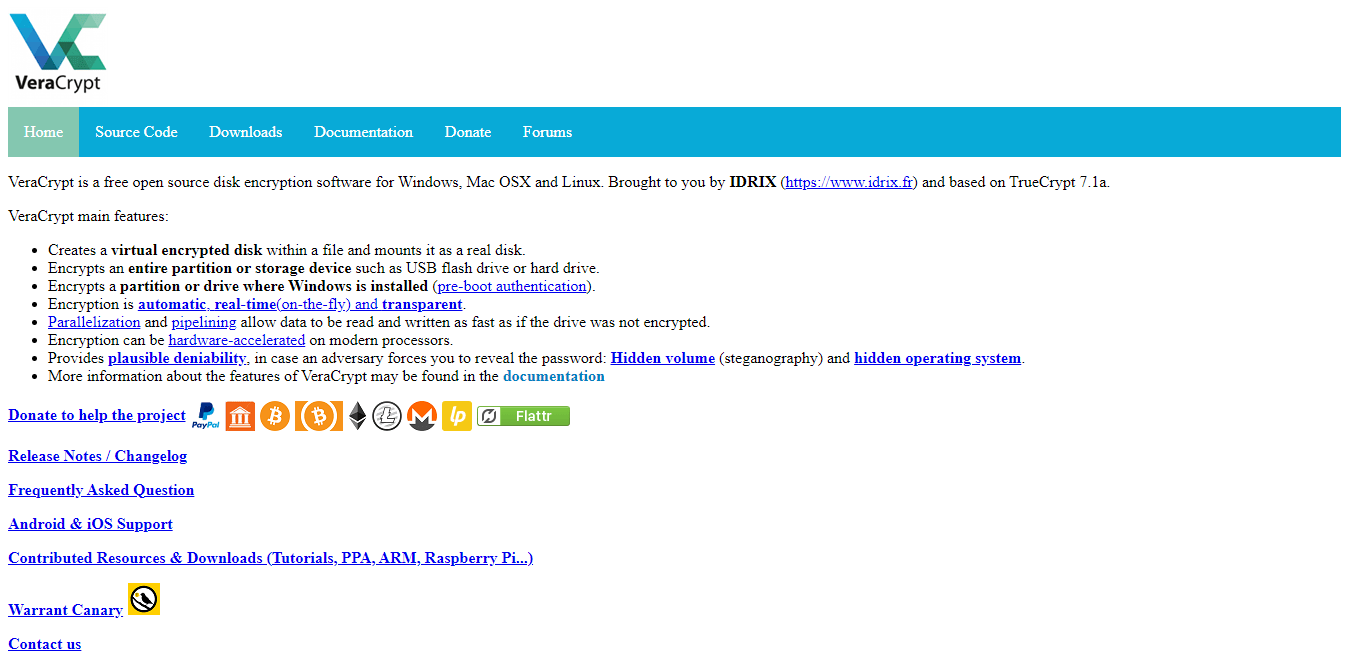
Most encryption software offers only very basic features on their free tier. But if you’re looking for feature-rich encryption software for free, VeraCrypt is an excellent option. The software is very intuitive. First, you’ll need to provide a few details, such as the data location and volume size. Then, the software encrypts the data for you.
VeraCrypt is an open-source software system with a vibrant community. Encryption enthusiasts will feel right at home using this software.
It’s also flexible, giving you a choice of encryption algorithms, including AES, Kuzbyechik, and Camellia. There’s even the option to layer encryption algorithms for tighter security. The software supports Mac, Windows, and Linux.
This flexibility also extends to how you encrypt your files. For example, you can encrypt your device at the operating system level. This means that unauthorized users can’t even turn on your machine. Alternatively, you can create an encrypted virtual disk. Anything you store in the virtual disk is automatically encrypted.
Finally, VeraCrypt allows you to encrypt and conceal existing storage devices, partitions, or drives. This option encrypts everything in the selected storage area.
This software is feature-rich, especially for a free platform. But it’s not the most beginner-friendly software, and there’s no option for support except for its open-source community.
Regardless, VeraCrypt is an excellent free solution, so it is easy to overlook its downsides.
IBM Guardium – Best Enterprise-Grade Encryption Software
Most of these solutions work well for individuals and SMBs. But enterprises may require more robust encryption features. IBM is an established business computing brand that offers its encryption product known as IBM Guardium.
You can tell this is an enterprise solution right off the bat. But, unfortunately, you cannot simply purchase a subscription from the IBM website. Instead, you’ll have to schedule a call with an IBM consultant to figure out your needs before you can get a quote.
This solution is perfect for organizations seeking to protect their databases. The software works for structured, semi-structured, and unstructured data. The solution’s capabilities include:
- Encryption
- Data discovery and classification
- Real-time monitoring and alerting
- Data security insights
- Automated compliance workflows
- Compliance reporting
- Vulnerability and risk assessments
Overall, Guardium is a powerful tool with terrific automation features. For example, the software monitors user patterns and can send an alert in case of suspicious activity. The software is also easy to use. So, you don’t need to be an IT expert despite this being an enterprise-grade solution.
The only main downside to IBM Guardium is its steep cost. It is hardly surprising given the software’s capabilities. But, it can be out of reach for many small and medium-sized businesses.
How to Pick Your Encryption Software
We’ve outlined what we think are the six best encryption software currently on the market. But, the best software for your specific needs isn’t always obvious. Fortunately, you can follow a few steps to ensure you make the right choice.
Step 1 – Decide Which Data to Encrypt
The typical organization features a constant flow of information between users. These users aren’t just limited to employees. There might also be consultants, contractors, vendors, and customers. But, it is impossible to encrypt all data, everywhere, all the time.
It is necessary to decide the specific type of data you’d like to secure. This way, you have a good idea of the encryption algorithm and accompanying software suitable for your needs. To this end, data classification will help you understand all of the information that you transmit and store. Then, you can categorize the data based on use, sensitivity, and regulatory impact.
The results of your data classification will inform the type of encryption you should use. For example, most software relies on symmetric encryption. This means that you use the same key to encrypt and decrypt information.
However, there are instances where asymmetric encryption is the better option. This type of encryption uses two keys, a public, and a private key. You use the public key to encrypt messages and a private one to decrypt them. If your company often requires confirming identity for digital signatures, a tool like AxCrypt Premium may be the best solution.
Step 2 – Decide on Your Must-Have Features
It’s much easier to identify your must-have features once you know which data you’d like to encrypt. Some of the critical elements to consider include:
- Secure Deletion – It’s no use encrypting files if you’ll end up keeping the original unencrypted file. Simply deleting the file the conventional way may not be secure, even if you bypass the recycle bin. There’s always the possibility that the deleted file can be recovered using forensic software. Therefore, you need a secure way to delete your original files permanently. Software that comes with a built-in shredder is ideal for this purpose. The shredder re-writes the original file not to be recovered after deleting.
- Two-Factor Authentication – A strong master password will help to protect your encrypted files. But it is always nice to have extra protection. Ideally, your encryption software should at least have two-factor authentication that you can turn on or off. Two-factor authentication requires a second credential other than your password. This credential may be a code sent to your phone.
- Filename Encryption – Encrypting your files means other users cannot access the information without a key. However, they can still see the file name and get a sense of the data you have on your computer. Filename encryption is a must-have if this is a concern for you. The software also encrypts your file names, which are incomprehensible to other users.
- Text Encryption – It may not be enough to encrypt your files. You may also want to send secure messages via email or instant messaging apps. Software with text encryption allows you to send messages confidentially. Only the intended recipient with a key will be able to decipher your message.
- Encryption Algorithm – This feature may not be an essential consideration for most novice users. As long as you use AES, you should be fine. But, it’s worth considering other algorithms such as Blowfish for its flexibility and speed or RSA if you prefer having a public and private key. Other algorithm options include Twofish and Triple DES. Or, you could choose a tool that offers multiple encryption options. Then, you can select your preferred option once you get familiar with how encryption works.
Step 3 – Consider Your Regulatory Compliance Requirements
Some compliance standard binds every business that collects data. These standards include:
- GDPR – For companies that do business in the European Union
- HIPPA – For organizations in healthcare
- PCI DSS – For businesses that deal with customer’s financial information
- CCPA – For organizations operating in California
Most encryption software paints a broad brush and supports these compliance requirements. But, it is worth double-checking that the encryption software meets the compliance regulations you are subject to. At the very least, you’ll need to ensure that your chosen software uses AES encryption.
Step 4 – Don’t Forget Cloud Encryption

Typically, you encrypt files before transferring them to the cloud. However, some solutions protect the data as it moves to and from cloud-based applications. Some software providers like NordLocker even provide secure cloud storage on their servers, in addition to encryption.
While most cloud services offer basic encryption, you also need to be proactive in protecting your sensitive information. This is because cloud services work on a shared responsibility model. This means that the service does its best to protect your data. But, you are equally responsible for protecting the data you store on the cloud.
Some software will even update and encrypt your cloud backups for free. This option is typically an add-on service.

